
Mastering Active Directory
Deploy and secure infrastructures with Active Directory, Windows Server 2016, and PowerShell, 2nd Edition
Dishan Francis
- 786 pages
- English
- ePUB (mobile friendly)
- Available on iOS & Android
Mastering Active Directory
Deploy and secure infrastructures with Active Directory, Windows Server 2016, and PowerShell, 2nd Edition
Dishan Francis
About This Book
Become an expert at managing enterprise identity infrastructure by leveraging Active DirectoryKey Features• Explore the new features in Active Directory Domain Service• Manage your Active Directory services for Windows Server 2016 effectively• Automate administrative tasks in Active Directory using PowerShell Core 6.xBook DescriptionActive Directory (AD) is a centralized and standardized system that automates networked management of user data, security, and distributed resources and enables inter-operation with other directories.This book will first help you brush up on the AD architecture and fundamentals, before guiding you through core components, such as sites, trust relationships, objects, and attributes. You will then explore AD schemas, LDAP, RMS, and security best practices to understand objects and components and how they can be used effectively. Next, the book will provide extensive coverage of AD Domain Services and Federation Services for Windows Server 2016, and help you explore their new features. Furthermore, you will learn to manage your identity infrastructure for a hybrid cloud setup. All this will help you design, plan, deploy, manage operations, and troubleshoot your enterprise identity infrastructure in a secure and effective manner. You'll later discover Azure AD Module, and learn to automate administrative tasks using PowerShell cmdlets. All along, this updated second edition will cover content based on the latest version of Active Directory, PowerShell 5.1 and LDAP.By the end of this book, you'll be well versed with best practices and troubleshooting techniques for improving security and performance in identity infrastructures.What you will learn• Design your Hybrid AD environment by evaluating business and technology requirements• Protect sensitive data in a hybrid environment using Azure Information Protection• Explore advanced functionalities of the schema• Learn about Flexible Single Master Operation (FSMO) roles and their placement• Install and migrate Active Directory from older versions to Active Directory 2016• Control users, groups, and devices effectively• Design your OU structure in the most effective way• Integrate Azure AD with Active Directory Domain Services for a hybrid setupWho this book is forIf you are an Active Directory administrator, system administrator, or network professional who has basic knowledge of Active Directory and is looking to become an expert in this topic, this book is for you.
Frequently asked questions
Information
Section 1: Active Directory Planning, Design, and Installation
- Chapter 1, Active Directory Fundamentals
- Chapter 2, Active Directory Domain Services 2016
- Chapter 3, Designing an Active Directory Infrastructure
- Chapter 4, Active Directory Domain Name System
- Chapter 5, Placing Operations Master Roles
- Chapter 6, Migrating to Active Directory 2016
Active Directory Fundamentals
- The Economist: https://www.economist.com/leaders/2017/05/06/the-worlds-most-valuable-resource-is-no-longer-oil-but-data
- Evening Standard: https://www.standard.co.uk/lifestyle/esmagazine/is-data-the-new-oil-how-information-became-the-fuel-of-the-future-a3740481.html
- The Australian: https://www.theaustralian.com.au/news/inquirer/the-new-oil-data-is-the-worlds-most-valuable-resource/news-story/f386217a9c63ac5ee6e1473413e90bda
- Forbes: https://www.forbes.com/sites/howardbaldwin/2015/03/23/drilling-into-the-value-of-data/#19693a5c65fa
- Benefits of using Active Directory
- Understanding Active Directory components
- Understanding Active Directory objects
- Active Directory server roles
- Azure AD
Benefits of using Active Directory
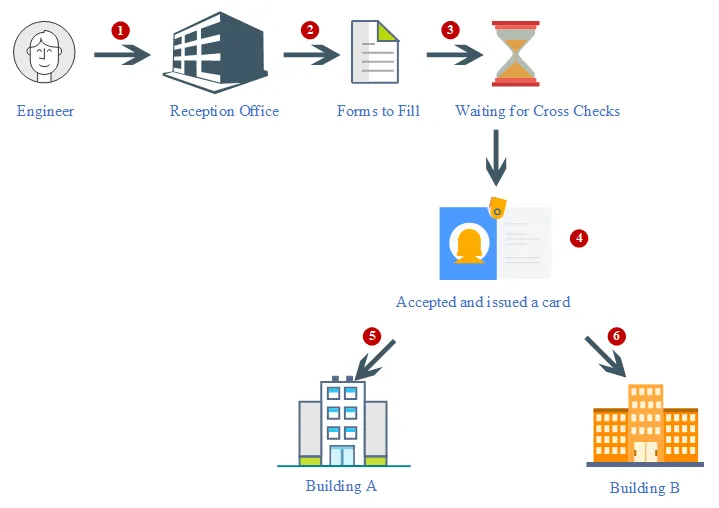
- The forms that the receptionist handed over to me contained certain questions to help her understand who I was. They were predefined questions, and I had to answer them in order to register my information in their system. Similar to this form, in a directory service we have to provide values for specific attributes.
- Once I had submitted the forms, she didn't hand over the magnetic card right away. She made a few calls to verify my identity, and also to confirm which buildings I would have access to. Then, my details were registered in the system, and it generated a magnetic card that had my photo and a barcode. With that, I became a part of their system, and that particular card was my unique identity within their organization. There would be no other visitor with the same barcode and identification number at the same time. Similarly, in a directory service, each identity is unique.
- If I needed to get access to buildings, I needed to tap the card at the entrance. Could I use my name or any other card to get through? No! The locking system of the building doors only recognized me if I presented the correct card. So, having a unique identity in their system was not enough; I needed to present it in the correct way to get the required access. Likewise, in an identity infrastructure, you need to validate your identity according to the method that the system had defined. It can be a username and password, a certificate, biometric information, and so on.
- I went to another building and tried to tap the card. Even when I used it correctly, the doors wouldn't open. The guard in the building asked for my card to check. Once I handed it over, he scanned it with a barcode reader and checked some information on his computer screen. Then he informed me that I was not allowed into that building, and he guided me to the correct building. This means that my information can be accessed from any building through their system in order to verify my identity and access permissions. In a similar way, in a directory, identities are saved in a central repository. This data can be accessed and verified from any system o...