
Mastering Metasploit,
Take your penetration testing and IT security skills to a whole new level with the secrets of Metasploit, 3rd Edition
Nipun Jaswal
- 492 pages
- English
- ePUB (mobile friendly)
- Available on iOS & Android
Mastering Metasploit,
Take your penetration testing and IT security skills to a whole new level with the secrets of Metasploit, 3rd Edition
Nipun Jaswal
About This Book
Discover the next level of network defense with the Metasploit framework
Key Features
- Gain the skills to carry out penetration testing in complex and highly-secured environments
- Become a master using the Metasploit framework, develop exploits, and generate modules for a variety of real-world scenarios
- Get this completely updated edition with new useful methods and techniques to make your network robust and resilient
Book Description
We start by reminding you about the basic functionalities of Metasploit and its use in the most traditional ways. You'll get to know about the basics of programming Metasploit modules as a refresher and then dive into carrying out exploitation as well building and porting exploits of various kinds in Metasploit.
In the next section, you'll develop the ability to perform testing on various services such as databases, Cloud environment, IoT, mobile, tablets, and similar more services. After this training, we jump into real-world sophisticated scenarios where performing penetration tests are a challenge. With real-life case studies, we take you on a journey through client-side attacks using Metasploit and various scripts built on the Metasploit framework.
By the end of the book, you will be trained specifically on time-saving techniques using Metasploit.
What you will learn
- Develop advanced and sophisticated auxiliary modules
- Port exploits from PERL, Python, and many more programming languages
- Test services such as databases, SCADA, and many more
- Attack the client side with highly advanced techniques
- Test mobile and tablet devices with Metasploit
- Bypass modern protections such as an AntiVirus and IDS with Metasploit
- Simulate attacks on web servers and systems with Armitage GUI
- Script attacks in Armitage using CORTANA scripting
Who this book is for
This book is a hands-on guide to penetration testing using Metasploit and covers its complete development. It shows a number of techniques and methodologies that will help you master the Metasploit framework and explore approaches to carrying out advanced penetration testing in highly secured environments.
Frequently asked questions
Information
Approaching a Penetration Test Using Metasploit

- The phases of penetration testing
- The basics of the Metasploit framework
- The workings of Metasploit exploit and scanner modules
- Testing a target network with Metasploit
- The benefits of using databases
- Pivoting and diving deep into internal networks
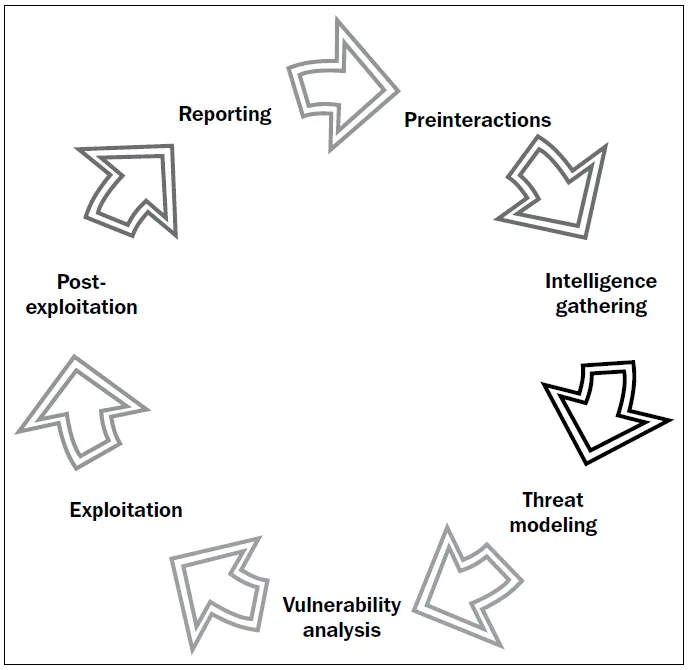
Organizing a penetration test
Preinteractions
- Scope: This section reviews the scope of the project and estimates the size of the project. The scope also defines what to include for testing and what to exclude from the test. The tester also discusses IP ranges and domains under the scope and the type of test (black box or white box). In case of a white box test, the tester discusses the kind of access and required credentials as well; the tester also creates, gathers, and maintains questionnaires for administrators. The schedule and duration of the test, whether to include stress testing or not, and payment, are included in the scope. A general scope document provides answers to the following questions:
- What are the target organization's most significant security concerns?
- What specific hosts, network address ranges, or applications should be tested?
- What specific hosts, network address ranges, or applications should explicitly NOT be tested?
- Are there any third parties that own systems or networks that are in the scope, and which systems do they hold (written permission must have been obtained in advance by the target organization)?
- Will the test be performed in a live production environment or a test environment?
- Will the penetration test include the following testing techniques: ping sweep of network ranges, a port scan of target hosts, vulnerability scan of targets, penetration of targets, application-level manipulation, client-side Java/ActiveX reverse engineering, physical penetration attempts, social engineering?
- Will the penetration test include internal network testing? If so, how will access be obtained?
- Are client/end user systems included in the scope? If so, how ...