Mastering Machine Learning for Penetration Testing
Develop an extensive skill set to break self-learning systems using Python
Chiheb Chebbi
- 276 pagine
- English
- ePUB (disponibile sull'app)
- Disponibile su iOS e Android
Mastering Machine Learning for Penetration Testing
Develop an extensive skill set to break self-learning systems using Python
Chiheb Chebbi
Informazioni sul libro
Become a master at penetration testing using machine learning with Python
Key Features
- Identify ambiguities and breach intelligent security systems
- Perform unique cyber attacks to breach robust systems
- Learn to leverage machine learning algorithms
Book Description
Cyber security is crucial for both businesses and individuals. As systems are getting smarter, we now see machine learning interrupting computer security. With the adoption of machine learning in upcoming security products, it's important for pentesters and security researchers to understand how these systems work, and to breach them for testing purposes.
This book begins with the basics of machine learning and the algorithms used to build robust systems. Once you've gained a fair understanding of how security products leverage machine learning, you'll dive into the core concepts of breaching such systems. Through practical use cases, you'll see how to find loopholes and surpass a self-learning security system.
As you make your way through the chapters, you'll focus on topics such as network intrusion detection and AV and IDS evasion. We'll also cover the best practices when identifying ambiguities, and extensive techniques to breach an intelligent system.
By the end of this book, you will be well-versed with identifying loopholes in a self-learning security system and will be able to efficiently breach a machine learning system.
What you will learn
- Take an in-depth look at machine learning
- Get to know natural language processing (NLP)
- Understand malware feature engineering
- Build generative adversarial networks using Python libraries
- Work on threat hunting with machine learning and the ELK stack
- Explore the best practices for machine learning
Who this book is for
This book is for pen testers and security professionals who are interested in learning techniques to break an intelligent security system. Basic knowledge of Python is needed, but no prior knowledge of machine learning is necessary.
Domande frequenti
Informazioni
Introduction to Machine Learning in Pentesting
- Machine learning models and algorithms
- Performance evaluation metrics
- Dimensionality reduction
- Ensemble learning
- Machine learning development environments and Python libraries
- Machine learning in penetration testing – promises and challenges
Technical requirements
- NumPy
- SciPy
- TensorFlow
- Keras
- pandas
- MatplotLib
- scikit-learn
- NLTK
- Theano
Artificial intelligence and machine learning
Machine learning models and algorithms
Supervised
Bayesian classifiers

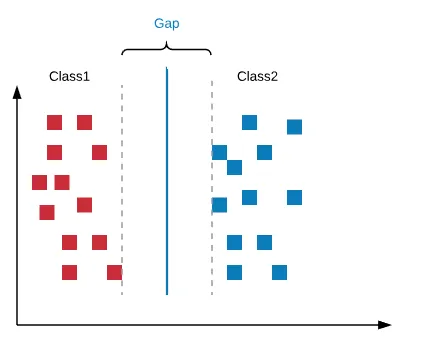
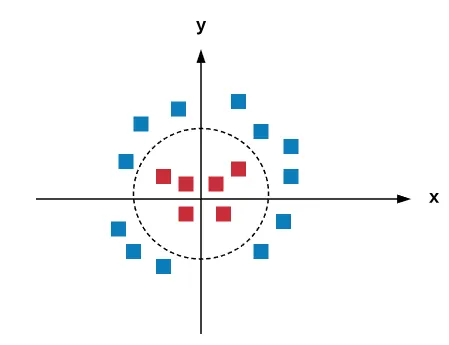
Support vector machines