Part I
Code and Cryptogram Strategies
In this part . . .
We introduce you to the world of cryptography, telling you about its history as well as its modern uses. Chapter 1 specifically highlights Masonic codes and ciphers.
In Chapter 2 we introduce you to many classic and modern types of ciphers, including some rare Masonic Ciphers that date back one or more centuries, and some new ciphers that are based on computer keyboards and cellphone keypads. Chapter 2 also contains all the instructions on how to solve the puzzles in this book.
Chapter 1
Clueing You In about Codes and Cryptograms
In This Chapter
Discovering cryptography through the ages Finding out about Masonic codes and ciphers Investigating additional resources In this book, we offer you the challenge of breaking several types of real ciphers and cryptograms, all devised by noted Australian puzzlemaster Denise Sutherland (author of Word Searches For Dummies [Wiley]).
In this chapter, we offer a few things to orient you to the secrets of codes and cryptograms, including the world of the cryptogram, the history of ciphers and codes, and the ways in which the time-honored fraternity of the Freemasons has used codes over the centuries. We also tell you about the contemporary world of codes and follow up by giving you some suggestions for further reading.
Introducing the Cryptographic World
The word cryptographic comes from elements that mean “hidden” (crypto) and “writing” (graph). The cryptographic world encompasses codes and ciphers (which we distinguish between in Chapter 2), which are used to create cryptograms (secret messages).
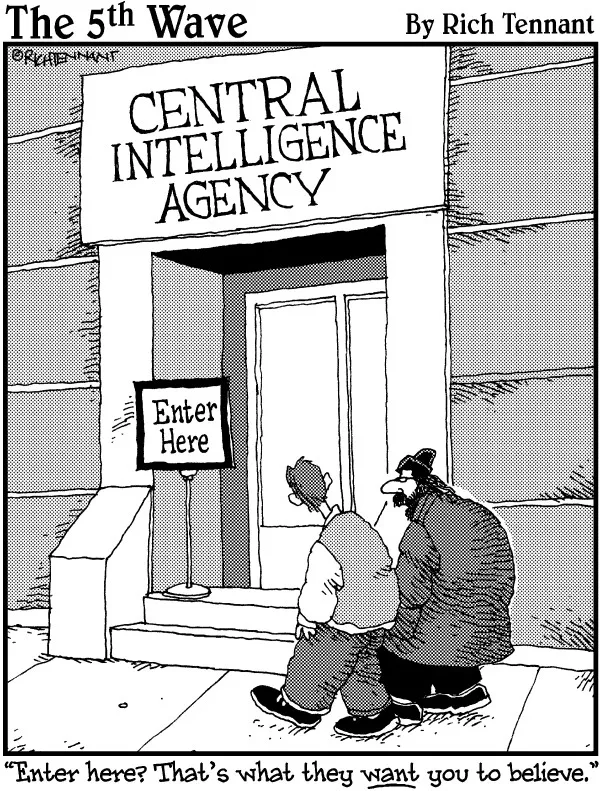
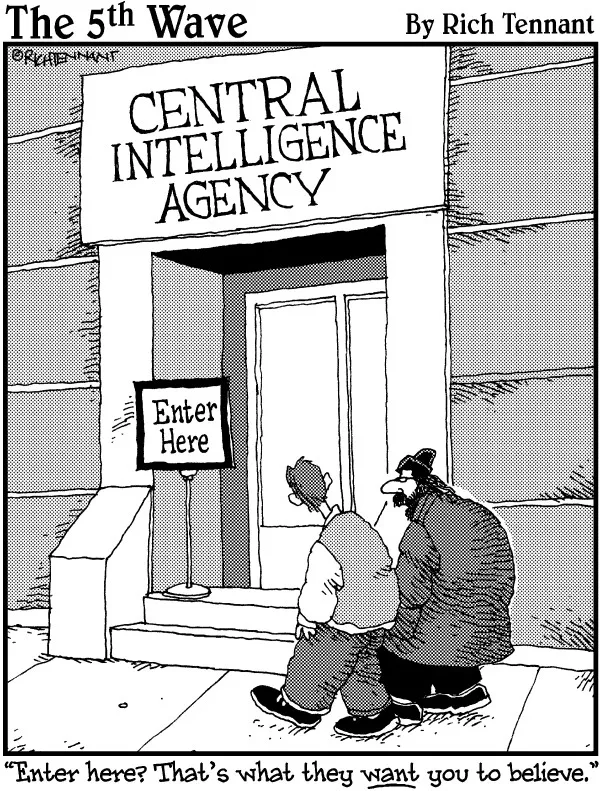
Ciphers. Codes. Cryptograms. What do you think about when you hear these words?
You may get an image of dark nights with fog-filled streets. In an attic in wartime London, a nervous man, constantly checking the door with anxious looks over his shoulder, is bent over a static-filled radio, writing down strings of numbers as they come over one particular frequency on the dial. In the street below, people in trench coats trade identical briefcases on street corners after an exchange of passwords. Such is the popular image — and, to some extent, the truth — of espionage, a world where ciphers, codes, and cryptograms are part of everyday reality.
Perhaps you prefer a more ancient or historical slant. Maybe you’re thinking of Julius Caesar sending messages to his troops in the hostile wilds of Western Europe, in the years before he ruled the Roman Empire. Perhaps you wonder about the secrets encoded on parchment in the Middle Ages and during the Renaissance by people who had quite a lot to lose — like their lives: political plotters, alchemists, and even — gasp! — practitioners of magic and sorcery. And then there are the secret societies of history, some political (the Black Hand of Serbia, the Holy Vehm, the Bavarian Illuminati), some criminal (the Black Hand of Sicily, La Cosa Nostra), some religious (the Rosicrucians), some fraternal (the Freemasons and their affiliated organizations, the York and Scottish Rites).
Then again, you may prefer a more modern and military approach. Military and diplomatic ciphers can make or break a nation in wartime. Just in the relatively short period of American history, ciphers and codes have played prominent roles in the American Revolutionary War and the War Between the States, and afterward. In the world at large, codes and ciphers — which ones were broken and which ones endured — had much to do with determining the outcomes of World Wars I and II, thus affecting the lives of billions of people. Your life may have been very different if the brave geniuses of Britain’s Bletchley Park group hadn’t broken the German Enigma ciphers.
Of course, today cryptography has gone corporate. You probably send or receive multiple encrypted messages every business day without even knowing it, as you transfer funds from an ATM to your pocket, as you order merchandise over the Internet, even as you communicate through telephone or e-mail. Keeping these communications secure is big business — and big trouble when it fails.
Considering the History of Codes and Ciphers
The origins of codes and ciphers — like the beginnings of language and writing, and my entire Beatles LP collection — are lost in the sands of time. David Kahn, the master historian of codes and ciphers, wrote that the development of secret writing was inevitable in any literate human culture because of “the multiple human needs and desires that demand privacy among two or more people.”
The...