Chapter 1
Knowing What Your Digital Devices Create, Capture, and Pack Away — Until Revelation Day
In This Chapter
Finding electronic evidence in the digital trails of our lives
Whipping your evidence into shape
Looking for evidence in the visible and invisible computer domain
Looking at the life cycle of a case
Think of computers, cell phones, PDAs, iPods, and other handheld devices as items with durable digital brains. Imagine that a detailed copy of every e-mail, text message, document, Internet upload or download, Google search, Facebook personal chat and posting, iPhone webChatter conversation, photo, financial transaction, and address book gets packed into electronic closets.
The amount of information left in each of these places is the basic reason that criminals are caught and found guilty and lawsuits are won or lost. When you use computer forensics tools to pick these digital brains or find skeletons in electronic closets, your case takes shape with e-evidence that’s tough to refute. Electronic evidence (e-evidence, for short) can play a starring role in the civil, criminal, matrimonial, or workplace cases you investigate. It’s as though people who use digital devices and social networks missed every CSI episode where incriminating e-mail, cell calls, and online activity became courtroom exhibits.
In this chapter, you become familiar with the locations and staying power of the all-too-accurate electronic records of actions, decisions, and indiscretions. You want to be smarter — or at least up to speed — with your opposition. For first responders to a crime scene and people planning litigation strategy, you learn how to answer your new call of duty. Methods used to hunt through hard drives and perform digital autopsies must be generally accepted by the legal system so that your results hold up. You need to be familiar, therefore, with rules of evidence, some legal-speak, and the concept of loopholes. And, you need good report-writing skills to explain the results of your cybersleuthing in simplified detail. If the case goes to trial, so do you as an expert witness. Testifying in court is about as much fun as one person can stand.
Living and Working in a Recorded World
Ever since the World Wide Web (WWW — the big one) dropped into our lives in 1991, rabid growth has taken place in the personal, professional, and criminal use of computers, the Internet, e-mail, wireless tech toys, and social networks. These devices create and capture greater amounts of “digital details” that are stored in more places than most people realize. You have less chance of destroying detail-trails perfectly than of committing the perfect crime. Like the fingerprint left on the seat adjustment of a car used in a crime, a rogue digital fingerprint always lives on to tell the tale.
Once in electronic form, almost all data, documents, and other file types can be analyzed offline of the application that produced it. Computer forensics software makes this process possible by converting an entire hard drive into a single searchable file — called an image — that has no hiding places.
Deleting is a misnomer
A hard drive is a big place, and data or other digital content from prior years may be retrievable in pristine condition even if someone has deleted it. In this section, we discuss how a computer operating system (OS) helps a file — and your investigation — survive.
Imagine that you compose a Word document and save it on your laptop with the filename Sand.doc. The process of saving a file on your hard disk involves three basic events:
- An entry is made into the File Allocation Table (FAT) to indicate the space where Sand.doc is stored in the Data Region. Like all files, Sand.doc is assigned (allocated) space on the hard drive. Those spaces are clusters. The FAT file system is supported by virtually all existing operating systems for personal computers.
- A directory entry is made to indicate Sand.doc as the filename, its size, link to the FAT, and some other information.
- Sand.doc is written to the data region. That is, it’s saved to a cluster on the hard drive. (Of course, files may occupy more than one cluster, but we’re keeping it simple.)
But when you decide to delete Sand.doc, only two events happen:
- The FAT entry for the file is zeroed out. That’s geek-speak for “the cluster that’s storing Sand.doc is declared digitally vacant and available to store another file.”
- The first character of the directory entry filename is changed to a special character so that the operating system knows to ignore it. In effect, it’s only pretending that the file isn’t there.
Like many deleted files, Sand.doc remains intact because nothing has been done to it. For Sand.doc to be totally overwritten and (almost) unrecoverable requires two events:
- The operating system must save another file (such as Water.doc) in the exact same cluster.
- Water.doc must be at least as large as Sand.doc.
A computer system never truly deletes files.
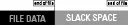
If, for example, Sand.doc filled an entire cluster and Water.doc file data took up less space, remnants of Sand.doc remain and are recoverable. The unused portion of the cluster is the slack space. More precisely, it’s the portion of the cluster not used by the new file. Figure 1-1 shows how the Sand file wasn’t dissolved (so to speak) by the Water file. Slack space cannot be seen without the specialized tools you find out about in Chapter 6.
When it comes to operating systems, remember these two concepts:
- You have no control over where the operating system saves files.
- The bigger the hard drive, the lower the probability that an existing deleted file will be overwritten.
Semisavvy criminals may try to outsmart the operating system by deleting the text, replacing it with non-incriminating content, and saving it with the same filename. But if they forget to account for the file size issue and compose a shorter file, remnants of the original file remain for recovery.