Ace the CompTIA Security+ exam with over 700 practice exam questions written using the style and format of the Security+ examKey Features• Get a detailed breakdown of the type of questions and the exam environment• Discover a step-by-step process that guides you through the study process week-by-week• Reinforce your learning by solving 100 questions for each domainBook DescriptionSecurity+ certification is the most popular entry-level certification for cybersecurity professionals. It has no work experience requirement, making it accessible to everyone willing to put in the time to prepare for the exam. Security+? Practice Tests are the perfect tools to prepare for the CompTIA Security+ exam.The first six chapters each cover one of the six Security+ domains. Each of those chapters contains around 100 practice test questions covering the material from that domain. The last two chapters each contain a full-length Security+ practice test that's designed to assess your readiness to take the actual test. At the end of each chapter, you'll find the answers to all of the questions along with detailed explanations to help reinforce your learning of the material.By the end of the book, you'll have enough practice to easily ace the CompTIA Security+ exam.What you will learn• Familiarize yourself with the format of the Security+ exam• Target your test preparation on each of the Security+ domains• Brush up on your understanding by testing yourself on realistic practice questions• Discover areas for improvement by comparing your responses to the answers provided• Measure your readiness with full-length practice tests• Know what to expect on test day and• Learn helpful strategies for tackling the different question typesWho this book is forThis book is designed for service desk analysts, system support engineers, and other IT professionals who want to start their career in managing the IT infrastructure of an organization. Basic knowledge of hardware, software, other relevant components of the IT industry will help you easily grasp the concepts explained in this book.
- 390 pages
- English
- ePUB (mobile friendly)
- Available on iOS & Android
eBook - ePub
Security+® Practice Tests
About this book
Trusted by 375,005 students
Access to over 1 million titles for a fair monthly price.
Study more efficiently using our study tools.
Information
1. Threats, Attacks, and Vulnerabilities
Domain 1 Questions
- After conducting a vulnerability scan of her network, Wendy discovered the issue shown here on several servers. What is the most significant direct impact of this vulnerability?
 Figure 1.1A. Attackers may eavesdrop on network communications.B. Attackers may use this information to gain administrative privileges.C. Encryption will not protect credentials for this account.D. Automated attacks are more likely to succeed.
Figure 1.1A. Attackers may eavesdrop on network communications.B. Attackers may use this information to gain administrative privileges.C. Encryption will not protect credentials for this account.D. Automated attacks are more likely to succeed. - Pete is investigating a domain hijacking attack against his company that successfully redirected web traffic to a third-party website. Which one of the following techniques is the most effective way to carry out a domain hijacking attack?A. ARP poisoningB. Network eavesdroppingC. DNS poisoningD. Social engineering
- Which one of the following characters is the most important to restrict when performing input validation to protect against XSS attacks?A. <B. !C. $D. '
- Darren is investigating an attack that took place on his network. When he visits the victim's machine and types www.mybank.com into the address bar, he is directed to a phishing site designed to look like a legitimate banking site. He then tries entering the IP address of the bank directly into the address bar and the legitimate site loads. What type of attack is likely taking place?A. IP spoofingB. DNS poisoningC. ARP spoofingD. Typosquatting
- Which one of the following technologies must be enabled on a wireless network for a Pixie Dust attack to succeed?A. SSID broadcastingB. WPSC. WPAD. WEP
- During forensic analysis, Drew discovered that an attacker intercepted traffic headed to networked printers by modifying the printer drivers. His analysis revealed that the attacker modified the code of the driver to transmit copies of printed documents to a secure repository. What type of attack took place?A. RefactoringB. ShimmingC. SwappingD. Recoding
- What type of scan can best help identify cases of system sprawl in an organization?A. Database scanB. Web application scanC. Detailed scanD. Discovery scan
- Scott is reviewing a list of cryptographic cipher suites supported by his organization's website. Which one of the following algorithms is not secure and may expose traffic to eavesdropping attacks?A. ECCB. 3DESC. AESD. DES
- Brenda is selecting the tools that she will use in a penetration test and would like to begin with passive techniques. Which one of the following is not normally considered a passive reconnaissance technique?A. Social engineeringB. Wireless network eavesdroppingC. Open source intelligenceD. Domain name searches
- Scott is a security administrator for a federal government agency. He recently learned of a website that advertises jobs for former government employees. When he accessed the site, the site launched code in his browser that attempted to install malicious software on his system. What type of attack took place?A. Denial of serviceB. Watering holeC. SpywareD. Trojan horse
- Paul received an email warning him that a new virus is circulating on the internet and that he needs to apply a patch to correct the problem. The message is branded with a Microsoft header. The virus message is actually a hoax and the patch contains malicious code. What principle of social engineering best describes what the attacker is trying to exploit by including the Microsoft header?A. ConsensusB. ScarcityC. TrustD. Intimidation
- Kristen conducts a vulnerability scan against her organization's network and discovers a file server with the vulnerability shown here. Which one of the following actions is the best way to remediate this vulnerability?
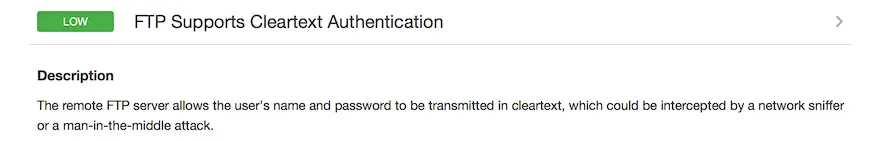 Figure 1.2A. Discontinue the file transfer serviceB. Require strong passwordsC. Switch to SFTPD. Require multifactor authentication
Figure 1.2A. Discontinue the file transfer serviceB. Require strong passwordsC. Switch to SFTPD. Require multifactor authentication - Frank is the new CISO at a mid-sized business. Upon entering his role, he learns that the organization has not conducted any security training for their sales team. Which one of the following attacks is most likely to be enabled by this control gap?A. Buffer overflowB. Social engineeringC. Denial of serviceD. ARP poisoning
- After conducting security testing, Bruce identifies a memory leak issue on one of his servers that runs an internally developed application. Which one of the following team members is most likely able to correct this issue?A. DeveloperB. System administratorC. Storage administratorD. Security analyst
- Greg recently detected a system on his network that occasionally begins sending streams of TCP SYN packets to port 80 at a single IP address for several hours and then stops. It later resumes, but directs the packets to a different address. What type of attack is taking place?A. Port scanningB. DDoSC. IP scanningD. SQL injection
- During a security assessment, Ryan learns that the Accounts Receivable department prints out records containing customer credit card numbers and files them in unlocked filing cabinets. Which one of the following approaches is most appropriate for resolving the security issues this situation raises?A. Physically secure paper recordsB. Encrypt sensitive informationC. Modify business processD. Monitor areas containing sensitive records
- Jaime is concerned that users in her organization may fall victim to DNS poisoning attacks. Which one of the following controls would be most helpful in protecting against these attacks?A. DNSSECB. Redundant DNS serversC. Off-site DNS serversD. Firewall rules
- Irene is reviewing the logs from a security incident and discovers many entries in her database query logs that appear similar to the ones shown here. What type of attack was attempted against her server?
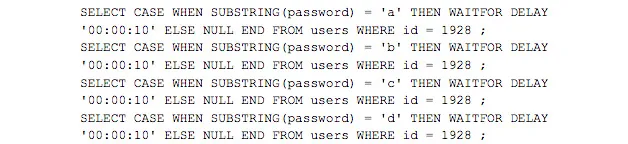 Figure 1.3A. Error-based SQL injectionB. Timing-based SQL injectionC. TOC/TOUD. LDAP injection
Figure 1.3A. Error-based SQL injectionB. Timing-based SQL injectionC. TOC/TOUD. LDAP injection - Carl is concerned that his organization's public DNS servers may be used in an amplification attack against a third party. What is the most effective way for Carl to prevent these servers from being used in an amplification attack?A. Disable open resolutionB. Block external DNS requestsC. Block internal DNS requestsD. Block port 53 at the firewall
- What is the purpose of a DNS amplification attack?A. Resource exhaustionB. Host redirectionC. Record poisoningD. Man-in-the-middle attack
- Angie is investigating a piece of malware found on a Windows system in her organization. She determines that the malware forced a running program to load code stored in a library. What term best describes this attack? A. DLL injectionB. SQL injectionC. Pointer dereferenceD. Buffer overflow
- Which one of the following threat sources is likely to have the highest level of sophistication?A. Organized crimeB. HacktivistC. APTD. Script kiddie
- In which of the following types of penetration test does the attacker not have any access to any information about the target environment prior to beginning the attack?A. Grey boxB. White boxC. Red boxD. Black box
- Bill is securing a set of terminals that are being used to access a highly sensitive web application. He would like to protect against a man-in-the-browser attack. Which one of the following actions would be most effective in meeting Bill's goal?A. Disabling browser extensionsB. Requiring multifactor authenticationC. Requiring TLS encryptionD. Disabling certificate pinning
- Kevin runs a vulnerability scan on a system on his network and identifies a SQL injection vulnerability. Which one of the following security controls is likely not present on the network?A. TLSB. DLPC. IDSD. WAF
- Maureen is implementing TLS encryption to protect transactions that are being run against her company's web services infrastructure. Which one of the following cipher suites would not be an appropriate choice?A. AES256-CCMB. ADH-RC4-MD5C. ECDHE-RSA-AES256-SHA384D. DH-RSA-AES256-GCM-SHA384
- Val runs a vulnerability scan of her network and finds issues similar to the one shown here on many systems. What action should Val take?
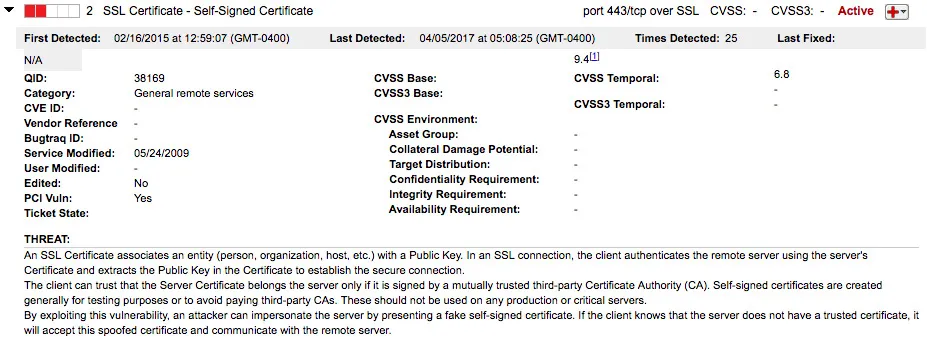 Figure 1.4A. Immediately replace all certificatesB. Conduct a risk assessmentC. No action is necessaryD. Replace certificates as they expire
Figure 1.4A. Immediately replace all certificatesB. Conduct a risk assessmentC. No action is necessaryD. Replace certificates as they expire - Barry would like to identify the mail server being used by an organization. Which one of the following DNS record types identifies a mail server?A. MXB. AC. CNAMED. SOA
- Gina runs a vulnerability scan of a server in her organization and receives the results shown here. What corrective action could Gina take to resolve these issues without disrupting the service?
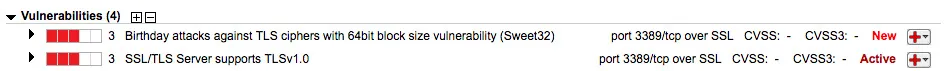 Figure 1.5A. Update RDP encryptionB. Update HTTPS encryptionC. Disable the network portD. No action is necessary
Figure 1.5A. Update RDP encryptionB. Update HTTPS encryptionC. Disable the network portD. No action is necessary - Carl is a help desk technician and received a call from an executive who received a suspicious email message. The content of the email appears as follows. What type of attack most likely took place?
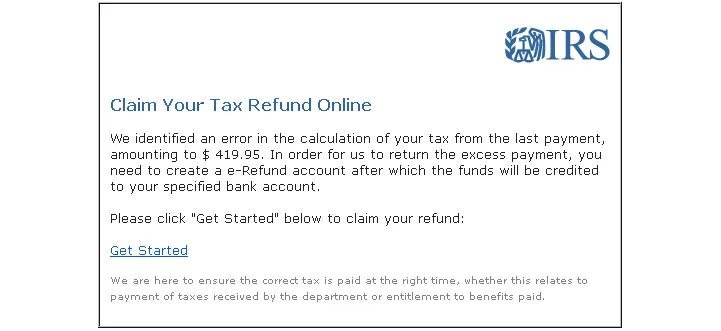 Figure 1.6A. WhalingB. Spear phishingC. VishingD. Phishing
Figure 1.6A. WhalingB. Spear phishingC. VishingD. Phishing - Dan is a cybersecurity analyst. Each day, he retrieves log files from a wide variety of security devices and correlates the information they contain, searching for unusual patterns of activity. What security control is likely lacking in Dan's environment?A. Firewall management toolsB. IPSC. SIEMD. NAC
- Which one of the following security controls would be MOST effective in combatting buffer overflow attacks?A. IDSB. VPNC. DLPD. ASLR
- Mary believes that her network was the target of a wireless networking attack. Based upon the Wireshark traffic capture shown here, what type of attack likely took place?
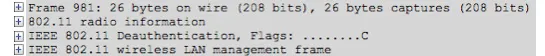 Figure 1.7A. DisassociationB. IV accumulationC. ReplayD. Bluesnarfing
Figure 1.7A. DisassociationB. IV accumulationC. ReplayD. Bluesnarfing - Gary is concerned about the susceptibility of his organization to phishing attacks. Which one of the following controls will best defend against this type of attack?A. EncryptionB. User trainingC. FirewallD. Background checks
- In which one of the following types of spoofing attack is the attacker often able to establish two-way communication with another device?A. Email spoofingB. MAC spoofingC. IP spoofingD. RFID spoofing
- Rob is conducting a penetration test against a wireless network and would like to gather network traffic containing successful authentication attempts, but the network is not heavily trafficked and he wants to speed up the information gathering process. What technique can he use?A. ReplayB. Brute forceC. Rainbow tableD. Disassociation
- Joe considers himself a hacker but generally does not develop his own exploits or customize exploits that have been developed by others. Instead, he downloads exploits from hacker sites and attempts to apply them to large numbers of servers around the internet until he finds one that is vulnerable. What type of hacker is Joe?A. 31337 h4x0rB. APTC. Script kiddieD. Penetration tester
- Julie is beginning a penetration test against a client and would like to begin with passive reconnaissance. Which one of the following tools may be used for pas...
Table of contents
- Preface
- 1. Threats, Attacks, and Vulnerabilities
- 2. Technologies and Tools
- 3. Architecture and Design
- 4. Identity and Access Management
- 5. Risk Management
- 6. Cryptography and PKI
- 7. Practice Exam 1
- 8. Practice Exam 2
Frequently asked questions
Yes, you can cancel anytime from the Subscription tab in your account settings on the Perlego website. Your subscription will stay active until the end of your current billing period. Learn how to cancel your subscription
No, books cannot be downloaded as external files, such as PDFs, for use outside of Perlego. However, you can download books within the Perlego app for offline reading on mobile or tablet. Learn how to download books offline
Perlego offers two plans: Essential and Complete
- Essential is ideal for learners and professionals who enjoy exploring a wide range of subjects. Access the Essential Library with 800,000+ trusted titles and best-sellers across business, personal growth, and the humanities. Includes unlimited reading time and Standard Read Aloud voice.
- Complete: Perfect for advanced learners and researchers needing full, unrestricted access. Unlock 1.4M+ books across hundreds of subjects, including academic and specialized titles. The Complete Plan also includes advanced features like Premium Read Aloud and Research Assistant.
We are an online textbook subscription service, where you can get access to an entire online library for less than the price of a single book per month. With over 1 million books across 990+ topics, we’ve got you covered! Learn about our mission
Look out for the read-aloud symbol on your next book to see if you can listen to it. The read-aloud tool reads text aloud for you, highlighting the text as it is being read. You can pause it, speed it up and slow it down. Learn more about Read Aloud
Yes! You can use the Perlego app on both iOS and Android devices to read anytime, anywhere — even offline. Perfect for commutes or when you’re on the go.
Please note we cannot support devices running on iOS 13 and Android 7 or earlier. Learn more about using the app
Please note we cannot support devices running on iOS 13 and Android 7 or earlier. Learn more about using the app
Yes, you can access Security+® Practice Tests by Mike Chapple in PDF and/or ePUB format, as well as other popular books in Computer Science & Cyber Security. We have over one million books available in our catalogue for you to explore.