![]()
CHAPTER 1: THE INTERNET
When you use the Internet you are potentially creating a path for an attacker to get into your personal space, or to get your information. There are security controls you can put in place and also a few key behaviours for using the Internet that will better protect your information.
1.1 Connecting
The first thing to do for the internet is secure the connection. The ways to connect to the internet are introduced here as it is logical to understand this before you connect, but they are explained in greater detail in later sections.
Home networks (section 5.1) – this connection is secured by the home network encryption (section 5.1) and secured by password or passphrase (section 5.1).
Mobile network (section 6.3) – this connection is generally used when you are mobile. This connection should be secured with a VPN (section 6.3) if you are accessing important information or using your payment card.
Public wi-fi (section 6.2) – this connection should be used whenever you are in a public place and using provided wi-fi. For example, airports, trains, buses, coffee shops, restaurants, etc. This connection is secured through a VPN.
Note. A VPN is a Virtual Private Network, it is a secure channel created between you and the target website.
1.2 Browsers
There are a number of browsers available that you can use to search the Internet. Each browser has a different profile, how well it integrates with search engines, how fast it responds to requests, what features are built in, how fast it takes to reload, how quickly it downloads, etc. Below are some of the more popular free browsers.
Mozilla Firefox
Mozilla Firefox has been around for a number of years but has never been a front-runner. The issues with Microsoft Internet Explorer have, however, led to an increase in the use of Firefox as a default browser.
Mozilla Firefox can be customised to your requirements, is fast and secure, and protects your privacy.
Google Chrome
Google Chrome is inarguably the most widely used browser, with a 60% share of the market. It is unique in that it applies a single sign-on managing a number of Cloud-based personal applications, including Gmail (email), a calendar and personal notes. Google Chrome is also an advanced browser in the way security is applied, using two-factor authentication through a person’s smartphone. Google Chrome is regularly updated.
Google Chrome is a fast browser but is not the quickest. It has strong security features and a very simple interface, and other features are available and easily installed.
Opera
This browser has a built-in VPN (see section 6.3 to understand the advantages of this), an ad blocker and a battery saver mode.
Microsoft Edge
This is the new browser from Microsoft that has been issued from Windows 10 onwards. It has a good interface, offers good security and supports extensions that can increase the number of functions.
Vivaldi
This browser is fully customisable, fast and ‘fun’ to use, although it lacks the features of other browsers.
Internet Explorer
This is probably the most widely known Internet browser, but some versions may cause unnecessary risk to home users. The latest versions of Internet Explorer – IE10 and IE11 – remain supported, but any new Windows operating systems will be released with Microsoft Edge, or any later browser Microsoft creates.
Supported or not supported – what does it mean?
If a browser is supported it means the developer will issue updates to fix vulnerabilities. If a browser is not supported, no updates will be issued. Whether a browser is supported is very important to the user’s security.
Regularly check the security of your browser. Make sure updates are applied.
Look at the settings in your browser. If necessary, research the settings and apply them to make your browser as secure as possible.
1.3 Browser history
One thing you can do to protect yourself online, especially when you are using a public or shared computer, is to delete your browser history. There are two ways to do this:
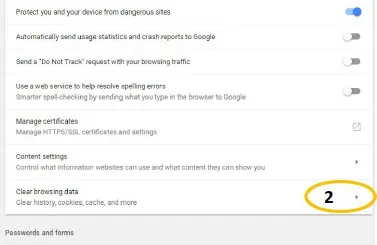
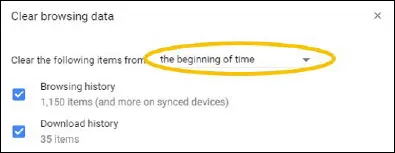
Permanently – this is done in the ‘Settings’ or ‘Options’. Within this menu there will be an option to ‘Clear browsing data’ when you close the browser. Within the ‘Clear browsing data’ menu there will also be options to clear cookies, cache and other groups such as download history and even stored passwords. All of these things should be selected for as far back as possible; some browsers may offer to do this for a certain period of time, be it hours, days or weeks, or ‘from the beginning of time’.
Session, when closing the browser – as well as the permanent option in the browser ‘Settings’ or ‘Option’s menu, there will be a ‘History’ tab that will allow you to clear the session browsing history. This will only clear the browsing history and is not nearly as effective as the permanent option.
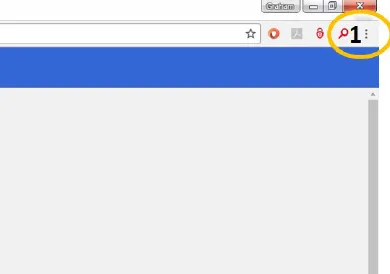
1. To clear your browsing history in Google Chrome go to the browser menu and select ‘Settings’ (3 vertical dots)
2. To clear history, go to ‘Clear browsing data’
3. Make sure you select ‘the beginning of time’ for all options and click ‘CLEAR BROWSING DATA’ as shown above.
1.4 Tabs
Many browsers allow you to open multiple tabs in a session, but this can create a chance for an attacker to get sensitive information. If an attacker has got access to your internet session, then they could potentially access all tabs you have open (a session is from when you open the internet browser until you close it).
Social networking sites are a preferred way for attackers to get access to your online session. By not doing your online banking in the same session as having a social networking site open there is less possibility the online banking session will be compromised or breached.
There are a few things you can do to prevent this.
Have a browser that you only use to access sites where sensitive information will be used.
Have a different browser for searches and other general web access, such as Facebook.
If you find an item to buy during a search, open the link to the chosen item in a new window to buy it, closing the first window before buying.
Do not open sensitive sites in the same session as general access, such as searches or Facebook.
One thing you could do is have multiple browsers. For example, you could have three browsers available on your system:
1. One to access sensitive information, such as banks, medical, social, shopping, etc.
2. One to manage your professional profile, email, LinkedIn, etc.
3. One for general things such as searches and to access your social network, Facebook, etc.
1.5 Search engine
There are a number of search engines available, with five introduced below. These five are considered the primary search engines. Each of these search engines are free to use.
As a rule, search engines are financed by advertising. Search engines will return sponsored pages as the initial results of your search, then return the results that appear to be most closely associated with your search topic or feature keywords from your search. There are a number of risks with search engines, with the main one being that you trust the search engine to return genuine and safe results. The search engine’s results are based on topic and/or keywords, so it is possible that the primary results are laden with malware or misinformation but have been built with keywords featured in ...