- 292 pages
- English
- ePUB (mobile friendly)
- Available on iOS & Android
eBook - ePub
Cyberspace and Cybersecurity
About this book
Providing comprehensive coverage of cyberspace and cybersecurity, this textbook not only focuses on technologies but also explores human factors and organizational perspectives and emphasizes why asset identification should be the cornerstone of any information security strategy. Topics include addressing vulnerabilities, building a secure enterprise, blocking intrusions, ethical and legal issues, and business continuity. Updates include topics such as cyber risks in mobile telephony, steganography, cybersecurity as an added value, ransomware defense, review of recent cyber laws, new types of cybercrime, plus new chapters on digital currencies and encryption key management.
Tools to learn more effectively

Saving Books

Keyword Search

Annotating Text

Listen to it instead
Information
1Vulnerabilities in Information Systems
Cyberspace: From terra incognita to terra nullius.
Introduction
Vulnerability in any system is the result of an intentional or unintentional omission or of an inadvertent design mistake that directly or indirectly leads to a compromise in the system’s availability, integrity, or confidentiality. In information assurance, vulnerabilities may hide in each level of security, be it information access security, computer and storage security, communications security, or operational and physical security. In the case of information systems, the major components are people, hardware, and software. Therefore, the presence of vulnerabilities must be sought in each of these three areas. Figure 1.1 illustrates the factors that contribute to a secure cyberspace and the expectations out of cybersecurity.
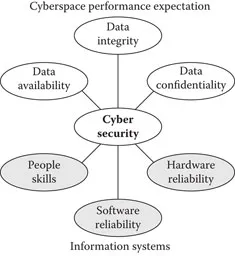
Figure 1.1Cybersecurity serving as the infrastructure of cyberspace.
Over half a century ago, designers, engineers, and scientists successfully quantified the concept of reliability for the design and maintenance of hardware and of software to a lesser extent. Today, efforts are being made to quantify the abstract concept of vulnerability as it applies to the security of information systems. The aim is to express the perceived level of security in a way that is measurable, standardized, and understood and to improve “… the measurability of security through enumerating baseline security data, providing standardized languages as means for accurately communicating the information, and encouraging the sharing of the information with users by developing repositories” [1].
Vulnerabilities can be hidden in data, code, and most often in processes that inadvertently allow unauthorized access. Intrusions, however, can occur not only in the Internet, but also in the intranets, where most often security is not as strong. Security can be strengthened through intelligent mechanisms of authentication applied at both ends—the user side as well as the server side.
At the user side, authentication can be greatly fortified with the introduction of additional mechanisms, such as one-time passwords (OTP), provided via intra- or extra-Internet channels [2]. Such channels can be biometrics, questionnaires, or additional transparent parameters related to the user device identification numbers, such as manufacturer’s serial number, Media Access Control (MAC), or International Mobile Equipment Identity (IMEI).
MAC, also referred to as Physical Address, is a 48-bit number, expressed as 12 hexadecimal digits, that uniquely identifies the network interface of the computer. The network interface circuit may be an insertable network card or may be embedded in the computer’s motherboard. Figure 1.2 shows how the MAC address of a personal computer can be identified.
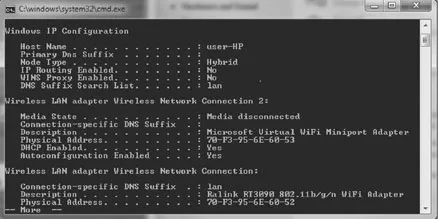
Figure 1.2MAC address in a personal computer, 70-F3-95-6E-60-52.
IMEI similarly uniquely identifies devices that utilize mobile telephony and is a number, usually 13 to 15 digits long. Mobile telephony providers assign a telephone number to devices linking them to their IMEI identification. Figure 1.3 illustrates the IMEI numbers available inside mobile phones.

Figure 1.3Mobile phone IMEI numbers.
In addition to the available MAC and IMEI numbers, device serial numbers and network parameters can also be used for authentication, such as intranet and Internet addresses. The above apply to client authentication toward the server.
At the server side, the use of certificates, IP restrictions, and data encapsulations can greatly enhance authentication and security. While in transit, data can be protected by hash codes, such as the cyclic redundancy code (CRC), and by the private key/public key encryption mechanisms.
Vulnerabilities in information systems can originate in a very wide variety of causes, ranging from firewall penetrations and Trojan horse attacks to decentralization and static resource allocation. Most frequently, vulnerabilities are introduced while systems are being upgraded or adapted to new operational environments.
Causes of Vulnerability
In the context of cybersecurity, vulnerability is a deficiency that can result in a performance degradation or system failure. Such deficiency may be in the application itself, or it may be in the hosting computer, in the network, or even in the user’s training deficiencies.
That’s why applications need to be continuously reviewed. Applications’ parameters, besides the software code itself, include the interfaces with the hosting system as well as interfaces with the users. Thus, the code must be replaced with the updated one, the hosting system’s new characteristics must be taken into account, and the user skills should be enhanced.
Patches provided by the developer must be immediately applied. Plus, applications designed for a certain version of an operating system may not necessarily operate with another, prior or later.
While an application in itself may be secure, its remote accessibility may be of weak controls, such as passwords or other authentication mechanisms, thus creating a system vulnerability.
Often an organization’s network is loaded with applications that inadvertently, and unintentionally, allow cross-accessing. That is, legitimate entry into one application allows backdoor entry into another. In this case, network segmentation is needed to eliminate such vulnerability. For example, the financial operations network and access points should be physically separated from the users’ access to products’ information.
It must be realized that protection, let it be for a country, for a house or for a database, has numerous parameters, each coming with a price tag. So, each shield of protection needs to pass a cost-effectiveness analysis, in order to optimize the...
Table of contents
- Cover
- Half Title Page
- Title Page
- Copyright Page
- Contents
- Foreword
- Preface
- Acknowledgments
- Author
- Chapter 1 Vulnerabilities in Information Systems
- Chapter 2 Vulnerabilities in the Organization
- Chapter 3 Risks in Information Systems Infrastructure
- Chapter 4 Secure Information Systems
- Chapter 5 Cybersecurity and the CIO
- Chapter 6 Building a Secure Organization
- Chapter 7 Cyberspace Intrusions
- Chapter 8 Cyberspace Defense
- Chapter 9 Cyberspace and the Law
- Chapter 10 Cyber Warfare and Homeland Security
- Chapter 11 Digital Currencies
- Chapter 12 Transformation of Traditional Crime into Cybercrime
- References
- Index
Frequently asked questions
Yes, you can cancel anytime from the Subscription tab in your account settings on the Perlego website. Your subscription will stay active until the end of your current billing period. Learn how to cancel your subscription
No, books cannot be downloaded as external files, such as PDFs, for use outside of Perlego. However, you can download books within the Perlego app for offline reading on mobile or tablet. Learn how to download books offline
Perlego offers two plans: Essential and Complete
- Essential is ideal for learners and professionals who enjoy exploring a wide range of subjects. Access the Essential Library with 800,000+ trusted titles and best-sellers across business, personal growth, and the humanities. Includes unlimited reading time and Standard Read Aloud voice.
- Complete: Perfect for advanced learners and researchers needing full, unrestricted access. Unlock 1.4M+ books across hundreds of subjects, including academic and specialized titles. The Complete Plan also includes advanced features like Premium Read Aloud and Research Assistant.
We are an online textbook subscription service, where you can get access to an entire online library for less than the price of a single book per month. With over 1 million books across 990+ topics, we’ve got you covered! Learn about our mission
Look out for the read-aloud symbol on your next book to see if you can listen to it. The read-aloud tool reads text aloud for you, highlighting the text as it is being read. You can pause it, speed it up and slow it down. Learn more about Read Aloud
Yes! You can use the Perlego app on both iOS and Android devices to read anytime, anywhere — even offline. Perfect for commutes or when you’re on the go.
Please note we cannot support devices running on iOS 13 and Android 7 or earlier. Learn more about using the app
Please note we cannot support devices running on iOS 13 and Android 7 or earlier. Learn more about using the app
Yes, you can access Cyberspace and Cybersecurity by George Kostopoulos in PDF and/or ePUB format, as well as other popular books in Computer Science & Computer Science General. We have over one million books available in our catalogue for you to explore.