eBook - ePub
No Tech Hacking
A Guide to Social Engineering, Dumpster Diving, and Shoulder Surfing
- 384 pages
- English
- ePUB (mobile friendly)
- Available on iOS & Android
eBook - ePub
No Tech Hacking
A Guide to Social Engineering, Dumpster Diving, and Shoulder Surfing
About this book
Johnny Long's last book sold 12,000 units worldwide. Kevin Mitnick's last book sold 40,000 units in North America.As the cliché goes, information is power. In this age of technology, an increasing majority of the world's information is stored electronically. It makes sense then that we rely on high-tech electronic protection systems to guard that information. As professional hackers, Johnny Long and Kevin Mitnick get paid to uncover weaknesses in those systems and exploit them. Whether breaking into buildings or slipping past industrial-grade firewalls, their goal has always been the same: extract the information using any means necessary. After hundreds of jobs, they have discovered the secrets to bypassing every conceivable high-tech security system. This book reveals those secrets; as the title suggests, it has nothing to do with high technology.• Dumpster DivingBe a good sport and don't read the two "D words written in big bold letters above, and act surprised when I tell you hackers can accomplish this without relying on a single bit of technology (punny). • TailgatingHackers and ninja both like wearing black, and they do share the ability to slip inside a building and blend with the shadows.• Shoulder SurfingIf you like having a screen on your laptop so you can see what you're working on, don't read this chapter.• Physical SecurityLocks are serious business and lock technicians are true engineers, most backed with years of hands-on experience. But what happens when you take the age-old respected profession of the locksmith and sprinkle it with hacker ingenuity?• Social Engineering with Jack WilesJack has trained hundreds of federal agents, corporate attorneys, CEOs and internal auditors on computer crime and security-related topics. His unforgettable presentations are filled with three decades of personal "war stories" from the trenches of Information Security and Physical Security. • Google HackingA hacker doesn't even need his own computer to do the necessary research. If he can make it to a public library, Kinko's or Internet cafe, he can use Google to process all that data into something useful.• P2P HackingLet's assume a guy has no budget, no commercial hacking software, no support from organized crime and no fancy gear. With all those restrictions, is this guy still a threat to you? Have a look at this chapter and judge for yourself.• People WatchingSkilled people watchers can learn a whole lot in just a few quick glances. In this chapter we'll take a look at a few examples of the types of things that draws a no-tech hacker's eye.• KiosksWhat happens when a kiosk is more than a kiosk? What happens when the kiosk holds airline passenger information? What if the kiosk holds confidential patient information? What if the kiosk holds cash?• Vehicle SurveillanceMost people don't realize that some of the most thrilling vehicular espionage happens when the cars aren't moving at all!
Trusted by 375,005 students
Access to over 1.5 million titles for a fair monthly price.
Study more efficiently using our study tools.
Information
Chapter 1 Dumpster Diving
Hackers pilfer secret data in lots of different ways, but did you they can suck sensitive data right off a corporate network without even touching the network? You might think I’m talking about wireless technology, which doesn’t require any “touching” at all, but I’m not. Be a good sport and don’t read the two “D” words written in big bold letters at the top of this page, and act surprised when I tell you hackers can accomplish this without relying on a single bit of technology (punny). Or, don’t play along, and pretend not to be surprised. In fact, maybe it’s better you go on thinking your personal or corporate secrets aren’t sitting exposed in a dumpster somewhere, waiting for a no-tech hacker to snatch them up. In that case you better just skip this chapter.
Introduction to Dumpster Diving
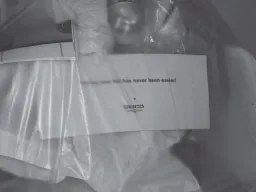
Dumpster diving involves … diving into dumpsters in search of valuable information. I know, it’s bad form to use the phrase in the definition of the phrase, but that’s what dumpster diving is, or what it used to be. These days, diving is optional. As this next photo shows, I find interesting stuff just hanging out in the open, waiting to be grabbed.

I find valuable trash in plain view all the time, like the insurance bill shown in the next photo, which is visible through the clear trash liner.
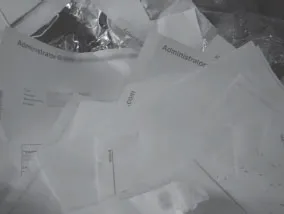
The next photo shows a pile of discarded documents belonging to a network administrator. I used my strong power of intuition to determine that these belonged to an administrator.
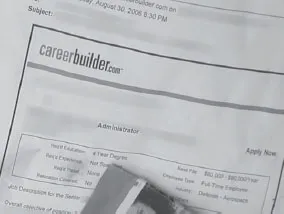
Judging from the next photo, “Fred” is obviously unhappy with his job—he’s hard at work surfing careerbuilder.com in search of a new position. This printout reveals an awful lot about Fred. What else can you tell me about him based on this single document?
For starters, it’s very probable that Fred’s got a four-year degree of some kind, otherwise he wouldn’t have printed out a job description that required that much schooling. It’s a good bet that he makes a good deal less than $80,000 a year, judging from the position’s salary, that he’s looking for a full-time gig, and that he’s probably working in the Defense Aerospace industry. Stuff like this makes me want to write Foreign Intelligence Service Recruiting for Dummies. Forget all the hard work of finding a mark’s name, email address, employer, educational background, department of defense affiliation and career aspirations. All it takes is a brainless dumpster sweep to find juicy recruiting targets.
Personal info is one thing, but I find sensitive corporate information all the time as well. The next photo shows a purchase order, detailing a company’s several thousand-dollar purchase.
Although the form is quite dated, it lists a great deal of information including the client’s name, address and phone number, a description of the service (which is technical in nature and reveals information about the inner workings of the client), and authorized management signatures (which may be of use to a forger if the manager is still employed with the service company).
A purchase order isn’t really a big deal, but I think the next document might be. It’s marked “Do Not Disseminate.”
Disseminate is such a big word that I think people might not understand what it means. This causes obvious problems when it comes time to discard (or should I say throw away) the document. Confusing phrases abound though, like proprietary information. I found it written on the next document which was lying on the ground outside a dumpster.
A clearer phrase to use might be “For Internal Use Only.” But even this phrase is obviously somewhat confusing, because I found it written on this now-famous dumpster dangling document.
I guess I miss the point of warning phrases like these. Inigo Montoya had it right in The Princess Bride when he said “You keep using that [phrase]. I do not think it means what you think it means.” I vote for banning confusing phrases like Proprietary Information and Do not disseminate. I vote for splashing every document with a clearer tagline like “Put In Parking Lot For Everyone To Read.” At least then there’s no confusion about what people are supposed to do when it comes time to throw the thing away.
And just in case you think it’s an awful lot of effort to walk past a dumpster and grab stuff that’s hanging out of it, I’ve got good news. Sometimes if you’re really lucky, all you have to do is stand in a parking lot on a windy day and wait for sensitive stuff to blow right into your face. That’s exactly what happened to my buddy Mike at work one day. He grabbed the offending document and after discovering it didn’t belong to his employer, he shared it with me. Now I’m sharing it with you.
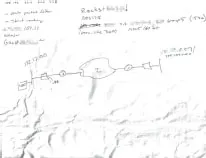
This bunch of scribble might not look like much to the untrained eye, but any techie will tell you that this map outlines everything needed to take control of a computer network. The (blurred) IP addresses is a real live address, and the username (admin) and password (blurred, beginning with the letters “G” and “a”) provide everything needed to log into the machine as an administrator. Another password (blurred, beginning with “R0ck3t”) written at the top of the page provides access to another private IP address (blurred, ending with “0.57”), and perhaps to other machines on the private network. The routing and subnet map along with terms like packet filter and strict routing reveal that the scribbler is technically adept, while terms like AES128, MD5 and ipsec indicate that he or she is at least somewhat security-conscious, but the simple fact remains that this document was tossed aside (along with other documents Mike didn’t bother to pluck out of the air) as if it were not important.
A high-tech attacker could spend hours, days, or weeks poking at the external box in an attempt to bypass AES-128 encryption and IPSEC to gain access to the private network behind it. Even then, he or she would struggle to bypass the security of the internal machines, to gain access to the “rocket” box. On the other hand, a no-tech hacker can bypass the security of the entire network in moments, just by peeling a document off his face and hanging on to it.
Fortunately, this kind of parking lot fodder is pretty rare. Admittedly, I’ve only seen a handful of cases that were this blatant. Most of the time I have to really push the limits and actually stick my head into the dumpster and peer inside. I discovered the next document in a dumpster on top of an open box of similar papers. The doc lists client names, account information, and a handy list of sales reps, the commissions they made and their Social Security numbers. A rival company might be interested in these documents, but an identity thief would have a field day with them.
When I found the dumpster shown in the next photo, I was disappointed because it had obviously just been emptied. The scattering of white envelopes left behind seemed innocuous enough, until I read the words healthcare information in bold red lettering. The rough, ripped edge of the envelope shown in the next photo seemed to suggest that some dummy had gotten the invoice in the mail, opened it, stuffed it back in the envelope and threw it out for a creepy (talented) no-tech hacker like me. If this were my invoice, I would have shredded it, then used the scraps to line my cat’s litter box—which seems to deter even the most dedicated of dumpster divers.
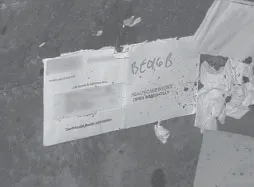
But the white envelope was not alone in this dumpster. I spotted a few more envelopes, each bearing the same scarlet lettering, and realized that each of the other envelopes (like the one sho...
Table of contents
- Cover
- Title Page
- Copyright
- Johnny Long, Author
- Technical Editor
- Contributing Author
- Foreword Contributor
- Special Contributors
- Foreword
- Introduction
- Table of Contents
- Chapter 1: Dumpster Diving
- Chapter 2: Tailgating
- Chapter 3: Shoulder Surfing
- Chapter 4: Physical Security
- Chapter 5: Social Engineering: Here’s How I Broke Into Their Buildings
- Chapter 6: Google Hacking Showcase
- Chapter 7: P2P Hacking
- Chapter 8: People Watching
- Chapter 9: Kiosks
- Chapter 10: Vehicle Surveillance
- Chapter 11: Badge Surveillance
- Top Ten Ways to Shut Down No-Tech Hackers
- Index
- Instructions for online access
Frequently asked questions
Yes, you can cancel anytime from the Subscription tab in your account settings on the Perlego website. Your subscription will stay active until the end of your current billing period. Learn how to cancel your subscription
No, books cannot be downloaded as external files, such as PDFs, for use outside of Perlego. However, you can download books within the Perlego app for offline reading on mobile or tablet. Learn how to download books offline
Perlego offers two plans: Essential and Complete
- Essential is ideal for learners and professionals who enjoy exploring a wide range of subjects. Access the Essential Library with 800,000+ trusted titles and best-sellers across business, personal growth, and the humanities. Includes unlimited reading time and Standard Read Aloud voice.
- Complete: Perfect for advanced learners and researchers needing full, unrestricted access. Unlock 1.5M+ books across hundreds of subjects, including academic and specialized titles. The Complete Plan also includes advanced features like Premium Read Aloud and Research Assistant.
We are an online textbook subscription service, where you can get access to an entire online library for less than the price of a single book per month. With over 1.5 million books across 990+ topics, we’ve got you covered! Learn about our mission
Look out for the read-aloud symbol on your next book to see if you can listen to it. The read-aloud tool reads text aloud for you, highlighting the text as it is being read. You can pause it, speed it up and slow it down. Learn more about Read Aloud
Yes! You can use the Perlego app on both iOS and Android devices to read anytime, anywhere — even offline. Perfect for commutes or when you’re on the go.
Please note we cannot support devices running on iOS 13 and Android 7 or earlier. Learn more about using the app
Please note we cannot support devices running on iOS 13 and Android 7 or earlier. Learn more about using the app
Yes, you can access No Tech Hacking by Johnny Long, Kevin D. Mitnick in PDF and/or ePUB format, as well as other popular books in Business & Human Resource Management. We have over 1.5 million books available in our catalogue for you to explore.