- 284 pages
- English
- ePUB (mobile friendly)
- Available on iOS & Android
eBook - ePub
Compressed Sensing in Li-Fi and Wi-Fi Networks
About this book
Compressed Sensing in Li-Fi and Wi-Fi Networks features coverage of the first applications in optical telecommunications and wireless. After extensive development of basic theory, many techniques are presented, such as non-asymptotic analysis of random matrices, adaptive detection, greedy algorithms, and the use of graphical models. The book can be used as a comprehensive manual for teaching and research in courses covering advanced signal processing, efficient data processing algorithms, and telecommunications. After a thorough review of the basic theory of compressed sensing, many mathematical techniques are presented, including advanced signal modeling, Nyquist sub-sampling of analog signals, the non-asymptotic analysis of random matrices, adaptive detection, greedy algorithms, and the use of graphical models.
- Offers extensive development of basic theory behind telecommunications and wireless networks
- Contains broad coverage of treat compressed sensing, including electromagnetism signals
- Provides insights into the two key areas of telecommunications, WIFI and LIFI
- Includes information on advanced signal modeling, Nyquist sub-sampling of analog signals, the non-asymptotic analysis of random matrices, adaptive detection, greedy algorithms, and more
Trusted by 375,005 students
Access to over 1.5 million titles for a fair monthly price.
Study more efficiently using our study tools.
Information
1
Shannon’s Theorem in Classic Data Processing
Abstract
Lombardi et al. give a comprehensive explanation of Shannon information. The question asked in their overview is: what is Shannon information? This chapter’s approach seems useful in measuring or understanding compressed sensing and a prelude on Shannon’s theorem is a necessary preliminary. Lombardi relies on numerous references: we highlight the work of Bell, Fisher, Khinchin, Kolmogorov and MacKay on data in general, without forgetting the depth of insight developed by Landauer.
Keywords
Capacity channel; Cryptography; Data Processing; Entropy; Sampling; Shannon’s theorem
1.1 Introduction
Lombardi et al. give a comprehensive explanation of Shannon information [LOM 16]. The question asked in their overview is: what is Shannon information? This chapter’s approach seems useful in measuring or understanding compressed sensing and a prelude on Shannon’s theorem is a necessary preliminary. Lombardi relies on numerous references: we highlight the work of Bell [BEL 57], Fisher [FIS 25], Khinchin [KHI 57], Kolmogorov [KOL 65, KOL 68, KOL 83] and MacKay [MAC 69] on data in general, without forgetting the depth of insight developed by Landauer [LAN 91, LAN 96].
It is traditionally accepted that Shannon’s seminal work on the data point in math is the paper in which he introduces a specific formalism designed to solve some specific technical problems [SHA 48] . Shannon entropy is considered with a given system’s statistical properties and the correlation between the states of two systems independently of their meaning or their semantic content. Shannon’s theorem is the basic ingredient of digital communication studies. Currently, the philosophy of data has posed a number of problems linked to the concept of data. The possibility of unifying these data theorems, the question of the logic of information, the relationship between data and thermodynamics, the significance of quantum data and links between data and calculation are crucial to a complete understanding of data.
We could assume that all questions about the meaning and interpretation of Shannon data have had clear and undisputable answers. However, this is not the case.
1.2 Shannon’s theorem
In his article on mathematical data theory [SHA 48], Shannon gave us specific results on the resources needed for optimal coding and error-free communication. Shannon’s theorem was then formalized by Khinchin [KHI 57].
According to Shannon [SHA 48], a general communication system is formed of the following five parts:
- – a source S that generates the message that should be received at the destination;
- – a transmitter T that transmits the message generated at the source into a signal that should be transmitted. Where data are coded, the coding is also implanted into this system;
- – a channel CH that is the medium used to transmit the signal from the transmitter to the receiver;
- – a receiver R that reconstructs the message from the signal;
- – a destination D that receives the message.
In Figure 1.1, we give an explicit schema of the system.

The source S is a system with an interval of possible states s 1,…sn usually called letters, whose respective probabilities of occurrence are p(s1),…,p(sn).
The quantity of information generated at the source through the occurrence of si can be defined as [SHA 48]:

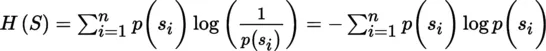
Since S produces sequences of states usually called messages, the source’s entropy s is defined as [SHA 48]:
By analogy, the destination D is a sy...
Table of contents
- Cover image
- Title page
- Table of Contents
- Dedication
- Copyright
- Preface
- List of Acronyms
- Introduction
- 1: Shannon’s Theorem in Classic Data Processing
- 2: Shannon’s Theorem in Quantum Data
- 3: Sparse Signals and Compressed Sensing
- 4: Compressed Sensing and the Fourier Transform
- 5: Compressed Sensing and Entanglement
- 6: [WITHDRAWN] Compressed Sensing and Intelligent LiFi Systems
- 7: Compressed Sensing in LiFi Systems in Mobile Communications and Cryptography
- 8: Compressed Sensing in WiFi Systems
- 9: Compressed Sensing in Interconnections Covering WiMAX, UMTS and MANET Satellite Networks
- 10: Compressed Sensing in Radar Interferometry
- 11: Compressed Sensing in Radars
- 12: Compressed Sensing in Electromagnetism
- Conclusion
- Bibliography
- Index
Frequently asked questions
Yes, you can cancel anytime from the Subscription tab in your account settings on the Perlego website. Your subscription will stay active until the end of your current billing period. Learn how to cancel your subscription
No, books cannot be downloaded as external files, such as PDFs, for use outside of Perlego. However, you can download books within the Perlego app for offline reading on mobile or tablet. Learn how to download books offline
Perlego offers two plans: Essential and Complete
- Essential is ideal for learners and professionals who enjoy exploring a wide range of subjects. Access the Essential Library with 800,000+ trusted titles and best-sellers across business, personal growth, and the humanities. Includes unlimited reading time and Standard Read Aloud voice.
- Complete: Perfect for advanced learners and researchers needing full, unrestricted access. Unlock 1.5M+ books across hundreds of subjects, including academic and specialized titles. The Complete Plan also includes advanced features like Premium Read Aloud and Research Assistant.
We are an online textbook subscription service, where you can get access to an entire online library for less than the price of a single book per month. With over 1.5 million books across 990+ topics, we’ve got you covered! Learn about our mission
Look out for the read-aloud symbol on your next book to see if you can listen to it. The read-aloud tool reads text aloud for you, highlighting the text as it is being read. You can pause it, speed it up and slow it down. Learn more about Read Aloud
Yes! You can use the Perlego app on both iOS and Android devices to read anytime, anywhere — even offline. Perfect for commutes or when you’re on the go.
Please note we cannot support devices running on iOS 13 and Android 7 or earlier. Learn more about using the app
Please note we cannot support devices running on iOS 13 and Android 7 or earlier. Learn more about using the app
Yes, you can access Compressed Sensing in Li-Fi and Wi-Fi Networks by Malek Benslama,Hatem Mokhtari in PDF and/or ePUB format, as well as other popular books in Technology & Engineering & Mobile & Wireless Communications. We have over 1.5 million books available in our catalogue for you to explore.