Set up next-generation firewalls from Palo Alto Networks and get to grips with configuring and troubleshooting using the PAN-OS platformKey Features• Understand how to optimally use PAN-OS features• Build firewall solutions to safeguard local, cloud, and mobile networks• Protect your infrastructure and users by implementing robust threat prevention solutionsBook DescriptionTo safeguard against security threats, it is crucial to ensure that your organization is effectively secured across networks, mobile devices, and the cloud. Palo Alto Networks' integrated platform makes it easy to manage network and cloud security along with endpoint protection and a wide range of security services. With this book, you'll understand Palo Alto Networks and learn how to implement essential techniques, right from deploying firewalls through to advanced troubleshooting. The book starts by showing you how to set up and configure the Palo Alto Networks firewall, helping you to understand the technology and appreciate the simple, yet powerful, PAN-OS platform. Once you've explored the web interface and command-line structure, you'll be able to predict expected behavior and troubleshoot anomalies with confidence. You'll learn why and how to create strong security policies and discover how the firewall protects against encrypted threats. In addition to this, you'll get to grips with identifying users and controlling access to your network with user IDs and even prioritize traffic using quality of service (QoS). The book will show you how to enable special modes on the firewall for shared environments and extend security capabilities to smaller locations. By the end of this network security book, you'll be well-versed with advanced troubleshooting techniques and best practices recommended by an experienced security engineer and Palo Alto Networks expert.What you will learn• Perform administrative tasks using the web interface and command-line interface (CLI)• Explore the core technologies that will help you boost your network security• Discover best practices and considerations for configuring security policies• Run and interpret troubleshooting and debugging commands• Manage firewalls through Panorama to reduce administrative workloads• Protect your network from malicious traffic via threat preventionWho this book is forThis book is for network engineers, network security analysts, and security professionals who want to understand and deploy Palo Alto Networks in their infrastructure. Anyone looking for in-depth knowledge of Palo Alto Network technologies, including those who currently use Palo Alto Network products, will find this book useful. Intermediate-level network administration knowledge is necessary to get started with this cybersecurity book.

- 514 pages
- English
- ePUB (mobile friendly)
- Available on iOS & Android
eBook - ePub
Mastering Palo Alto Networks
About this book
Trusted by 375,005 students
Access to over 1.5 million titles for a fair monthly price.
Study more efficiently using our study tools.
Information
Section 1: First Steps and Basic Configuration
In this section, you’ll learn about the core technologies that make up the Palo Alto Networks next-generation firewall, and how to connect to a freshly booted firewall appliance or virtual machine. You’ll also learn how to apply the basic configuration for you to get up and running.
This section comprises the following chapters:
- Chapter 1, Understanding the Core Technologies
- Chapter 2, Setting Up a New Device
Chapter 1: Understanding the Core Technologies
In this chapter, we're going to examine the core technologies that make up the Palo Alto Networks firewall.
We are going to take a closer look at how security zones control how security, Network Address Translation (NAT), and routing verdicts are made. We will review the mechanics behind App-ID and Content-ID so you get a deeper understanding of how packets are processed and security decisions are made by the firewall, and we will review how User-ID contributes to a more robust security stance by applying group-based or user-based access control.
This chapter will cover the following topics:
- Understanding the zone-based firewall
- Understanding App-ID and Content-ID
- The management and data plane
- Authenticating users with User-ID
Technical requirements
For this chapter, no physical installation is required; the technology is only explained. It is helpful if you've already worked with Palo Alto Networks firewalls, but it is not required. Some experience with firewalls or web proxies in general is recommended, as this will make the subject matter more tangible.
Understanding the zone-based firewall
Traditionally, when considering the firewall as an element of your network, most likely you will imagine a network design like the one in the following image, with two to four areas surrounding a box. Most of the time, whatever is placed in the north is considered dangerous, east and west are somewhat grey areas, and the south is the happy place where users do their daily tasks. The box in the middle is the firewall.
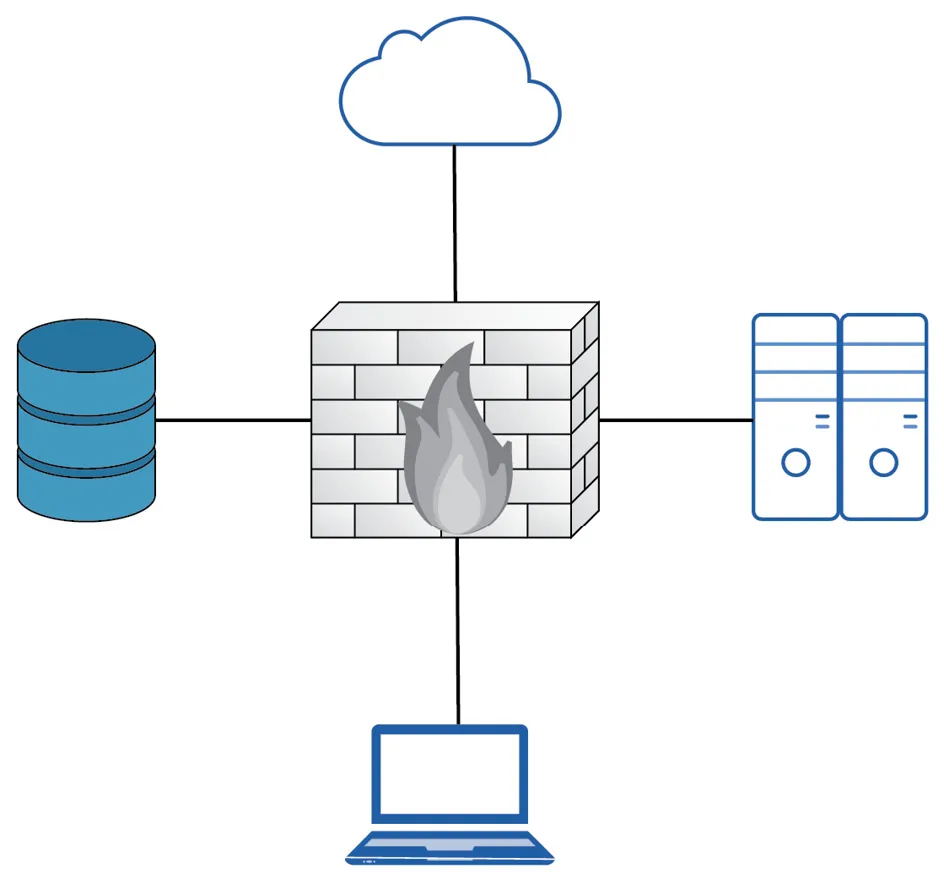
Figure 1.1 – Basic network topology
In reality, a network design may look a lot more complex due to network segregation, segmentation, remote offices being connected to the headquarters via all sorts of different technologies, and the adoption of cloud vendors.
In a route-based firewall, zones are simply an architectural or topological concept that helps identify which areas comprise the global network that is used by the company and are usually represented by tags that can be attached to a subnet object. They hold no bearing in any of the security decisions made by the system when processing security policies.
The zone-based firewall, on the other hand, will use zones as a means to internally classify the source and destination in its state table. When a packet is first received, a source zone lookup is performed. If the source zone has a protection profile associated with it, the packet is evaluated against the profile configuration. If the first packet is a TCP packet, it will also be evaluated against TCP state where the first packet needs to be a SYN packet, and a SYN-cookie is triggered if the protection profile threshold is reached. Then, a destination zone is determined by checking the Policy-Based Forwarding (PBF) rules and if no results are found, the routing table is consulted. Lastly, the NAT policy is evaluated as the destination IP may be changed by a NAT rule action, thereby changing the destination interface and zone in the routing table. This would require a secondary forwarding lookup to determine the post-NAT egress interface and zone:

Figure 1.2 – Phases of packet processing
After these zone lookups have been performed, the firewall will continue to the security policy evaluation.
The policy evaluation then uses the 'six tuple' (6-Tuple) to match establishing sessions to security rules:
- Source IP
- Source Port
- Destination IP
- Destination Port
- Source Zone
- Protocol
Zones are attached to a physical, virtual, or sub interface. Each interface can only be part of one single zone. Zones can be created to suit any naming convention and can be very descriptive in their purpose (untrust, dmz, lan, and so on), which ensures that from an administrative standpoint, each area is easily identifiable.
It is best practice to use zones in all security rules and leveraging a clear naming convention prevents misconfiguration and makes security rules very readable. Networks that are physically separated for whatever reason but are supposed to be connected topologically (for example, users spread over two buildings that come into the firewall on two separate interfaces) can be combined into the same zone, which simplifies policies.
It is important to note that there are implied rules that influence intra- or interzone sessions. These rules can be found at the bottom of the security policy:
- Default intrazone connections: Packets flowing from and to the same zone will be implicitly allowed.
- Default interzone connections: Packets flowing from one zone to a different zone are implicitly blocked.
Security rules can also be set to only accept traffic within the same zone, between different zones only, or both. This way, an administrator could set a specific rule for the intrazone setting and allow all applications without inadvertently allowing this full access to be open to a different network. Adding a second zone to that same rule would allow the same access inside the new zone, but there would not be any access granted between the zones; that would require a new interzone or universal rule:
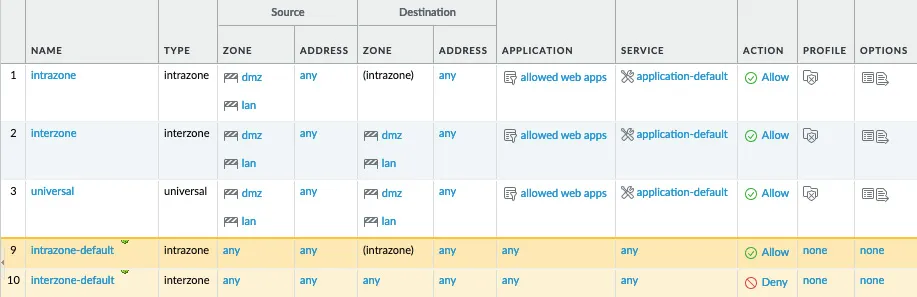
Figure 1.3 – Different security rule types and default rules
Let's now look at the expected behavior when determining zones.
Expected behavior when determining zones
When a packet arrives on an interface, the PBF policy or routing table will be consulted to determine the destination zone based on the original IP address in the packet header.
Let's consider the following routing table:
> show routing route
flags: A:active, ?:loose, C:connect, H:host, S:static, ~:internal, R:rip, O:ospf, B:bgp,
Oi:ospf intra-area, Oo:ospf inter-area, O1:ospf ext-type-1, O2:ospf ext-type-2, E:ecmp, M:multicast
VIRTUAL ROUTER: default (id 1)
==========
destination nexthop metric flags interface
0.0.0.0/0 198.51.100.1 10 A S ethernet1/1
198.51.100.0/24 198.51.100.2 0 A C ethernet1/1
198.51.100.2/32 0.0.0.0 0 A H
192.168.0.0/24 192.168.0.1 0 A C ethernet1/2
192.168.0.1/32 0.0.0.0 0 A H
172.16.0.0/24 172.16.0.1 0 A C ethernet1/3
172.16.0.1/32 0.0.0.0 0 A H
total routes shown: 7
Let's assume ethernet1/1 is the external interface with IP address 198.51.100.2 set to zone external, ethernet1/2 is the DMZ interface with IP address 192.168.0.1 set to zone dmz, and ethernet1/3 is the LAN interface with IP 172.16.0.1 and set to zone lan. The default route is going out of interf...
Table of contents
- Mastering Palo Alto Networks
- Why subscribe?
- Preface
- Section 1: First Steps and Basic Configuration
- Chapter 1: Understanding the Core Technologies
- Chapter 2: Setting Up a New Device
- Section 2: Advanced Configuration and Putting the Features to Work
- Chapter 3: Building Strong Policies
- Chapter 4: Taking Control of Sessions
- Chapter 5: Services and Operational Modes
- Chapter 6: Identifying Users and Controlling Access
- Chapter 7: Managing Firewalls through Panorama
- Section 3: Maintenance and Troubleshooting
- Chapter 8: Upgrading Firewalls and Panorama
- Chapter 9: Logging and Reporting
- z: VPN and Advanced Protection
- Chapter 11: Troubleshooting Common Session Issues
- Chapter 12: A Deep Dive into Troubleshooting
- Chapter 13: Supporting Tools
- Other Books You May Enjoy
Frequently asked questions
Yes, you can cancel anytime from the Subscription tab in your account settings on the Perlego website. Your subscription will stay active until the end of your current billing period. Learn how to cancel your subscription
No, books cannot be downloaded as external files, such as PDFs, for use outside of Perlego. However, you can download books within the Perlego app for offline reading on mobile or tablet. Learn how to download books offline
Perlego offers two plans: Essential and Complete
- Essential is ideal for learners and professionals who enjoy exploring a wide range of subjects. Access the Essential Library with 800,000+ trusted titles and best-sellers across business, personal growth, and the humanities. Includes unlimited reading time and Standard Read Aloud voice.
- Complete: Perfect for advanced learners and researchers needing full, unrestricted access. Unlock 1.5M+ books across hundreds of subjects, including academic and specialized titles. The Complete Plan also includes advanced features like Premium Read Aloud and Research Assistant.
We are an online textbook subscription service, where you can get access to an entire online library for less than the price of a single book per month. With over 1.5 million books across 990+ topics, we’ve got you covered! Learn about our mission
Look out for the read-aloud symbol on your next book to see if you can listen to it. The read-aloud tool reads text aloud for you, highlighting the text as it is being read. You can pause it, speed it up and slow it down. Learn more about Read Aloud
Yes! You can use the Perlego app on both iOS and Android devices to read anytime, anywhere — even offline. Perfect for commutes or when you’re on the go.
Please note we cannot support devices running on iOS 13 and Android 7 or earlier. Learn more about using the app
Please note we cannot support devices running on iOS 13 and Android 7 or earlier. Learn more about using the app
Yes, you can access Mastering Palo Alto Networks by Tom Piens in PDF and/or ePUB format, as well as other popular books in Computer Science & Client-Server Computing. We have over 1.5 million books available in our catalogue for you to explore.