- 286 pages
- English
- ePUB (mobile friendly)
- Available on iOS & Android
Modern Cryptography for Cybersecurity Professionals
About this book
As a cybersecurity professional, discover how to implement cryptographic techniques to help your organization mitigate the risks of altered, disclosed, or stolen dataKey Features• Discover how cryptography is used to secure data in motion as well as at rest• Compare symmetric with asymmetric encryption and learn how a hash is used• Get to grips with different types of cryptographic solutions along with common applicationsBook DescriptionIn today's world, it is important to have confidence in your data storage and transmission strategy. Cryptography can provide you with this confidentiality, integrity, authentication, and non-repudiation. But are you aware of just what exactly is involved in using cryptographic techniques? Modern Cryptography for Cybersecurity Professionals helps you to gain a better understanding of the cryptographic elements necessary to secure your data. The book begins by helping you to understand why we need to secure data and how encryption can provide protection, whether it be in motion or at rest. You'll then delve into symmetric and asymmetric encryption and discover how a hash is used. As you advance, you'll see how the public key infrastructure (PKI) and certificates build trust between parties, so that we can confidently encrypt and exchange data. Finally, you'll explore the practical applications of cryptographic techniques, including passwords, email, and blockchain technology, along with securely transmitting data using a virtual private network (VPN). By the end of this cryptography book, you'll have gained a solid understanding of cryptographic techniques and terms, learned how symmetric and asymmetric encryption and hashed are used, and recognized the importance of key management and the PKI.What you will learn• Understand how network attacks can compromise data• Review practical uses of cryptography over time• Compare how symmetric and asymmetric encryption work• Explore how a hash can ensure data integrity and authentication• Understand the laws that govern the need to secure data• Discover the practical applications of cryptographic techniques• Find out how the PKI enables trust• Get to grips with how data can be secured using a VPNWho this book is forThis book is for IT managers, security professionals, students, teachers, and anyone looking to learn more about cryptography and understand why it is important in an organization as part of an overall security framework. A basic understanding of encryption and general networking terms and concepts is needed to get the most out of this book.
Trusted by 375,005 students
Access to over 1 million titles for a fair monthly price.
Study more efficiently using our study tools.
Information
Section 1: Securing Our Data
- Chapter 1, Protecting Data in Motion or at Rest
- Chapter 2, The Evolution of Ciphers
- Chapter 3, Evaluating Network Attacks
Chapter 1: Protecting Data in Motion or at Rest
- Outlining the current threat landscape
- Understanding security services
- Introducing common cryptographic concepts
- Outlining substitution and transposition
Outlining the current threat landscape
Digitally transforming our world
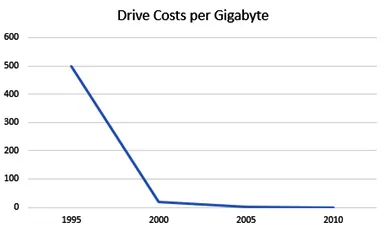
Rapidly advancing technology
- Voice over Internet Protocol (VoIP), also known as IP telephony, is a group of technologies primarily used to transmit phone calls over the internet
- Documents such as spreadsheets, word processor documents, presentation files, and Portable Document Format (PDF) files
- Images that include Joint Photographic Group (JPG), Tagged Image File Format (TIPP), and Bitmap Image File (BMP)
- Video that includes a wide range of formats, such as Moving Picture Experts Group (MPEG) and Advanced Video Coding (AVC), originating from a variety of sources
Table of contents
- Modern Cryptography for Cybersecurity Professionals
- Contributors
- Preface
- Section 1: Securing Our Data
- Chapter 1: Protecting Data in Motion or at Rest
- Chapter 2: The Evolution of Ciphers
- Chapter 3: Evaluating Network Attacks
- Section 2: Understanding Cryptographic Techniques
- Chapter 4: Introducing Symmetric Encryption
- Chapter 5: Dissecting Asymmetric Encryption
- Chapter 6: Examining Hash Algorithms
- Section 3: Applying Cryptography in Today's World
- Chapter 7: Adhering to Standards
- Chapter 8: Using a Public Key Infrastructure
- Chapter 9: Exploring IPsec and TLS
- Chapter 10: Protecting Cryptographic Techniques
- Assessments
- Other Books You May Enjoy
Frequently asked questions
- Essential is ideal for learners and professionals who enjoy exploring a wide range of subjects. Access the Essential Library with 800,000+ trusted titles and best-sellers across business, personal growth, and the humanities. Includes unlimited reading time and Standard Read Aloud voice.
- Complete: Perfect for advanced learners and researchers needing full, unrestricted access. Unlock 1.4M+ books across hundreds of subjects, including academic and specialized titles. The Complete Plan also includes advanced features like Premium Read Aloud and Research Assistant.
Please note we cannot support devices running on iOS 13 and Android 7 or earlier. Learn more about using the app