Explore the world of modern human-operated ransomware attacks, along with covering steps to properly investigate them and collecting and analyzing cyber threat intelligence using cutting-edge methods and toolsKey Features• Understand modern human-operated cyber attacks, focusing on threat actor tactics, techniques, and procedures• Collect and analyze ransomware-related cyber threat intelligence from various sources• Use forensic methods and tools to reconstruct ransomware attacks and prevent them in the early stagesBook DescriptionRansomware attacks have become the strongest and most persistent threat for many companies around the globe. Building an effective incident response plan to prevent a ransomware attack is crucial and may help you avoid heavy losses. Incident Response Techniques for Ransomware Attacks is designed to help you do just that.This book starts by discussing the history of ransomware, showing you how the threat landscape has changed over the years, while also covering the process of incident response in detail. You'll then learn how to collect and produce ransomware-related cyber threat intelligence and look at threat actor tactics, techniques, and procedures. Next, the book focuses on various forensic artifacts in order to reconstruct each stage of a human-operated ransomware attack life cycle. In the concluding chapters, you'll get to grips with various kill chains and discover a new one: the Unified Ransomware Kill Chain.By the end of this ransomware book, you'll be equipped with the skills you need to build an incident response strategy for all ransomware attacks.What you will learn• Understand the modern ransomware threat landscape• Explore the incident response process in the context of ransomware• Discover how to collect and produce ransomware-related cyber threat intelligence• Use forensic methods to collect relevant artifacts during incident response• Interpret collected data to understand threat actor tactics, techniques, and procedures• Understand how to reconstruct the ransomware attack kill chainWho this book is forThis book is for security researchers, security analysts, or anyone in the incident response landscape who is responsible for building an incident response model for ransomware attacks. A basic understanding of cyber threats will be helpful to get the most out of this book.
- 228 pages
- English
- ePUB (mobile friendly)
- Available on iOS & Android
eBook - ePub
Incident Response Techniques for Ransomware Attacks
About this book
Trusted by 375,005 students
Access to over 1 million titles for a fair monthly price.
Study more efficiently using our study tools.
Information
Section 1: Getting Started with a Modern Ransomware Attack
The first part of this book will help you to build a solid understanding of the modern ransomware threat landscape and how to properly plan your incident response activities.
This section comprises the following chapters:
- Chapter 1, The History of Human-Operated Ransomware Attacks
- Chapter 2, The Life Cycle of a Human-Operated Ransomware Attack
- Chapter 3, The Incident Response Process
Chapter 1: The History of Human-Operated Ransomware Attacks
Just like COVID-19, human-operated ransomware attacks became the second pandemic in 2020. Unfortunately, this trend keeps evolving nowadays. Despite the fact some threat actors announce their retirement, their places in the cybercrime business are quickly occupied by the younger generation.
Such attacks are discussed a lot nowadays; however, they emerged even before well-known ransomware outbreaks, such as WannaCry and NotPetya. Unlike those uncontrolled ransomware outbreaks, this time it's under the full control of various ransomware operators and their affiliates. Careful reconnaissance of compromised infrastructure, preparing it for final ransomware deployment, can potentially bring them millions of dollars in cryptocurrency.
Of course, there are multiple notable examples of ransomware strains used in human-operated attacks. In this chapter, we'll focus on the most important examples from a historic point of view, finishing on what's most common for today's threat landscape – ransomware-as-a-service programs.
We'll look at the following examples:
- 2016 – SamSam ransomware
- 2017 – BitPaymer ransomware
- 2018 – Ryuk ransomware
- 2019-present – ransomware-as-a-service programs
2016 – SamSam ransomware
These ransomware operators emerged in early 2016 and changed the ransomware threat landscape drastically. They didn't focus on regular users and single devices; instead, they attacked various companies, focusing on a human-operated approach, moving laterally and encrypting as many devices as possible, including those with the most important data.
The targets were very different and included the healthcare industry, the education sector, and even whole cities. A notable example was the city of Atlanta, Georgia, which took place in March 2018. As the result, the city had to pay approximately $2.7 million to contractors to recover its infrastructure.
The group commonly exploited vulnerabilities in public-facing applications, for example, JBOSS systems, or just brute-forced RDP-servers to gain the initial foothold to the target network.
To elevate privileges, the threat actors used a number of common hacking tools and exploits, including the notorious Mimikatz, so they could obtain domain administrator credentials.
Having elevated credentials, SamSam operators just scanned the network to obtain information about available hosts, then copied a piece of ransomware to each of them and ran it with help of another very common dual-use tool – PsExec.
The attackers had a payment website in the dark web. A victim could find all the necessary information on file decryption in the ransom note generated by the ransomware, as shown in Figure 1.1:

Figure 1.1 – SamSam ransom note example
Being active from 2016 to 2018, the group earned approximately $6 million, according to Sophos (source: https://www.sophos.com/en-us/medialibrary/PDFs/technical-papers/SamSam-The-Almost-Six-Million-Dollar-Ransomware.pdf).
Who was behind the SamSam ransomware
On November 28, 2018, the FBI unsealed an indictment charging Faramarz Shahi Savandi and Mohammad Mehdi Shah Mansouri with deploying SamSam ransomware internationally:
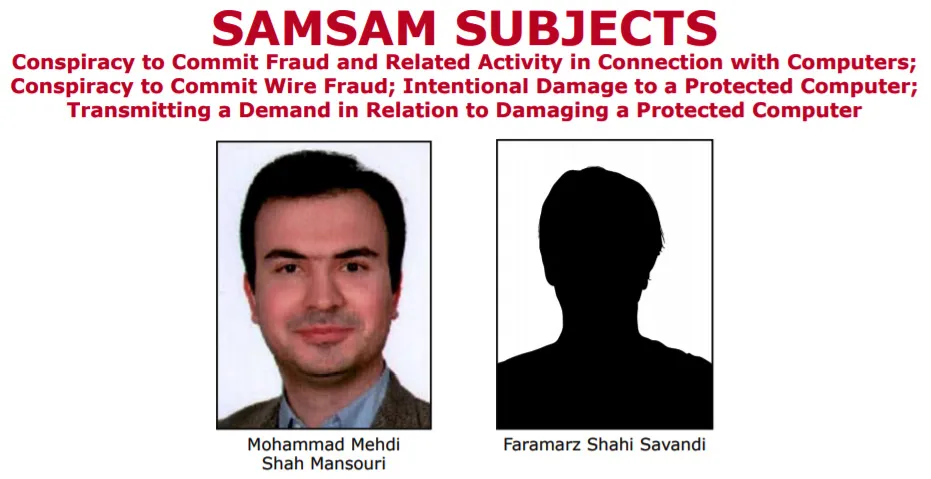
Figure 1.2 – An excerpt from an FBI Wanted poster
Both subjects are from Iran. After the indictment was unsealed, the threat actors managed to finish their malicious activities, at least under the name SamSam.
These threat actors showed others that enterprise ransomware attacks may be very profitable, so more and more groups emerged. One example is the BitPaymer ransomware.
2017 – BitPaymer ransomware
The BitPaymer ransomware is associated with Evil Corp – a cybercrime group believed to be of Russian origin. This ransomware strain introduced another trend in human-operated attacks – Big Game Hunting.
Everything started in August 2017, when BitPaymer operators successfully attacked a few hospitals from the NHS Lanarkshire board, demanding the astronomical ransom payment of $230,000 or 53 BTC.
To obtain the initial access to the target network, the group leveraged their long-standing tool – the Dridex trojan. The trojan allowed them to load PowerShell Empire – a popular post-exploitation framework – so the threat actor could move laterally through the network, and obtain elevated credentials, including with the use of Mimikatz, just like the SamSam operators.
To deploy the ransomware enterprise-wide, the threat actors leveraged a Group Policy modification, which allowed them to push a script on each host to run a piece of ransomware.
As the means of communication, the threat actors offered both emails and online chats; both could be found in the ransom note:
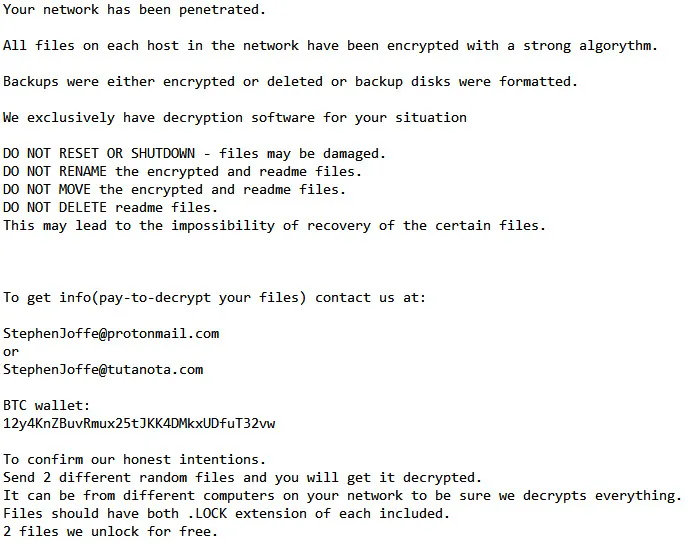
Figure 1.3 – BitPaymer ransom note example
In June 2019, a new ransomware was born from BitPaymer, called DoppelPaymer. It is believed that this specific ransomware was operated by a spin-off group from Evil Corp (source: https://www.crowdstrike.com/blog/doppelpaymer-ransomware-and-dridex-2/).
The mastermind behind the BitPaymer ransomware
On November 13, 2019, the FBI released an indictment charging Maksim Viktorovich Yakubets and Igor Olegovich Turashev with managing Dridex trojan operations:

Figure 1.4 – Excerpts from FBI Wanted posters
Maksim Viktorovich Yakubets is currently wanted for multiple counts of cybercriminal activity. According to various sources, it is stated that there is a $5 million reward for the apprehension of Maksim. Of course, Dridex was not the only trojan used in human-operated ransomware attacks. Another notable example is Trickbot, which is tightly connected to the Ryuk ransomware.
2018 – Ryuk ransomware
The Ryuk ransomware took Big Game Hunting to new heights. Associated with the Trickbot group, also known as Wizard Spider, this ransomware strain is st...
Table of contents
- Incident Response Techniques for Ransomware Attacks
- Contributors
- Preface
- Section 1: Getting Started with a Modern Ransomware Attack
- Chapter 1: The History of Human-Operated Ransomware Attacks
- Chapter 2: The Life Cycle of a Human-Operated Ransomware Attack
- Chapter 3: The Incident Response Process
- Section 2: Know Your Adversary: How Ransomware Gangs Operate
- Chapter 4: Cyber Threat Intelligence and Ransomware
- Chapter 5: Understanding Ransomware Affiliates' Tactics, Techniques, and Procedures
- Chapter 6: Collecting Ransomware-Related Cyber Threat Intelligence
- Section 3: Practical Incident Response
- Chapter 7: Digital Forensic Artifacts and Their Main Sources
- Chapter 8: Investigating Initial Access Techniques
- Chapter 9: Investigating Post-Exploitation Techniques
- Chapter 10: Investigating Data Exfiltration Techniques
- Chapter 11: Investigating Ransomware Deployment Techniques
- Chapter 12: The Unified Ransomware Kill Chain
- Other Books You May Enjoy
Frequently asked questions
Yes, you can cancel anytime from the Subscription tab in your account settings on the Perlego website. Your subscription will stay active until the end of your current billing period. Learn how to cancel your subscription
No, books cannot be downloaded as external files, such as PDFs, for use outside of Perlego. However, you can download books within the Perlego app for offline reading on mobile or tablet. Learn how to download books offline
Perlego offers two plans: Essential and Complete
- Essential is ideal for learners and professionals who enjoy exploring a wide range of subjects. Access the Essential Library with 800,000+ trusted titles and best-sellers across business, personal growth, and the humanities. Includes unlimited reading time and Standard Read Aloud voice.
- Complete: Perfect for advanced learners and researchers needing full, unrestricted access. Unlock 1.4M+ books across hundreds of subjects, including academic and specialized titles. The Complete Plan also includes advanced features like Premium Read Aloud and Research Assistant.
We are an online textbook subscription service, where you can get access to an entire online library for less than the price of a single book per month. With over 1 million books across 990+ topics, we’ve got you covered! Learn about our mission
Look out for the read-aloud symbol on your next book to see if you can listen to it. The read-aloud tool reads text aloud for you, highlighting the text as it is being read. You can pause it, speed it up and slow it down. Learn more about Read Aloud
Yes! You can use the Perlego app on both iOS and Android devices to read anytime, anywhere — even offline. Perfect for commutes or when you’re on the go.
Please note we cannot support devices running on iOS 13 and Android 7 or earlier. Learn more about using the app
Please note we cannot support devices running on iOS 13 and Android 7 or earlier. Learn more about using the app
Yes, you can access Incident Response Techniques for Ransomware Attacks by Oleg Skulkin in PDF and/or ePUB format, as well as other popular books in Computer Science & Computer Networking. We have over one million books available in our catalogue for you to explore.