- 528 pages
- English
- ePUB (mobile friendly)
- Available on iOS & Android
Mastering Cyber Intelligence
About this book
Develop the analytical skills to effectively safeguard your organization by enhancing defense mechanisms, and become a proficient threat intelligence analyst to help strategic teams in making informed decisionsKey Features• Build the analytics skills and practices you need for analyzing, detecting, and preventing cyber threats• Learn how to perform intrusion analysis using the cyber threat intelligence (CTI) process• Integrate threat intelligence into your current security infrastructure for enhanced protectionBook DescriptionThe sophistication of cyber threats, such as ransomware, advanced phishing campaigns, zero-day vulnerability attacks, and advanced persistent threats (APTs), is pushing organizations and individuals to change strategies for reliable system protection. Cyber Threat Intelligence converts threat information into evidence-based intelligence that uncovers adversaries' intents, motives, and capabilities for effective defense against all kinds of threats.This book thoroughly covers the concepts and practices required to develop and drive threat intelligence programs, detailing the tasks involved in each step of the CTI lifecycle. You'll be able to plan a threat intelligence program by understanding and collecting the requirements, setting up the team, and exploring the intelligence frameworks. You'll also learn how and from where to collect intelligence data for your program, considering your organization level. With the help of practical examples, this book will help you get to grips with threat data processing and analysis. And finally, you'll be well-versed with writing tactical, technical, and strategic intelligence reports and sharing them with the community.By the end of this book, you'll have acquired the knowledge and skills required to drive threat intelligence operations from planning to dissemination phases, protect your organization, and help in critical defense decisions.What you will learn• Understand the CTI lifecycle which makes the foundation of the study• Form a CTI team and position it in the security stack• Explore CTI frameworks, platforms, and their use in the program• Integrate CTI in small, medium, and large enterprises• Discover intelligence data sources and feeds• Perform threat modelling and adversary and threat analysis• Find out what Indicators of Compromise (IoCs) are and apply the pyramid of pain in threat detection• Get to grips with writing intelligence reports and sharing intelligenceWho this book is forThis book is for security professionals, researchers, and individuals who want to gain profound knowledge of cyber threat intelligence and discover techniques to prevent varying types of cyber threats. Basic knowledge of cybersecurity and network fundamentals is required to get the most out of this book.
Trusted by 375,005 students
Access to over 1 million titles for a fair monthly price.
Study more efficiently using our study tools.
Information
Section 1: Cyber Threat Intelligence Life Cycle, Requirements, and Tradecraft
- Chapter 1, Cyber Threat Intelligence Life Cycle
- Chapter 2, Requirements and Intelligent Team Implementation
- Chapter 3, Cyber Threat Intelligence Frameworks
- Chapter 4, Cyber Threat Intelligence Tradecraft and Standards
- Chapter 5, Goal Setting, Procedures for CTI Strategy, and Practical Use Cases
Chapter 1: Cyber Threat Intelligence Life Cycle
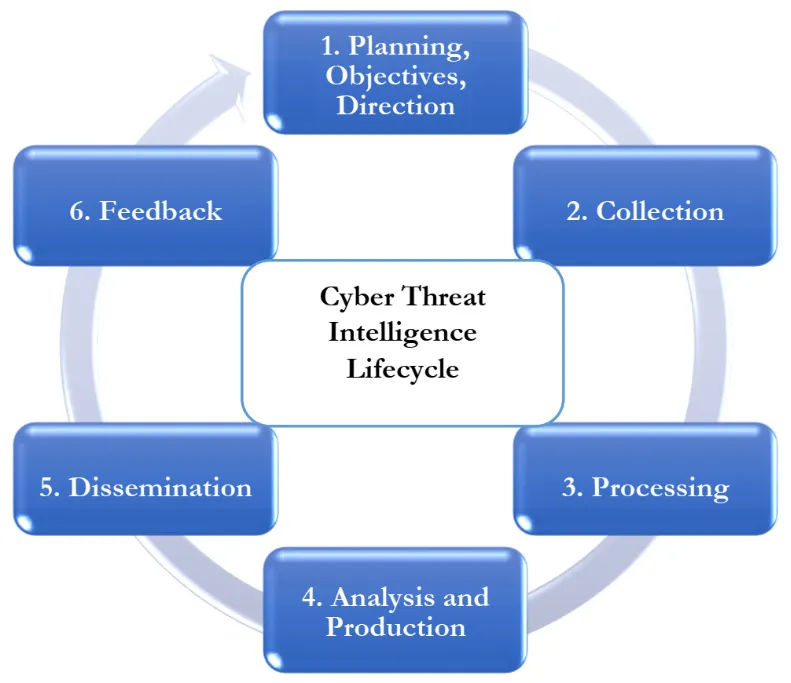
- Clearly explain what cyber threat intelligence is, why organizations must integrate it into the business and security team, who benefits from it, and be able to define its scope.
- Understand the challenges related to threat intelligence and cybersecurity in general.
- Know and understand the required components to effectively plan and set directions for a threat intelligence project.
- Know and understand the data required to build an intelligence project and how to acquire it globally.
- Understand intelligence data processing, why it is essential in integrating a CTI project, and justify the need for automating the processing step.
- Understand the analysis step, its application, and its impact on the entire CTI project. In this step, you will also learn about intelligence analysis bias and different techniques that can be used to avoid a biased intelligence analysis.
- Explain the cycle's dissemination step and how to share an intelligence product with the relevant stakeholders. You should also understand the importance of the audience when consuming the product.
- Understand and explain the feedback phase of the cycle and state why it is critical in the project.
- Cyber threat intelligence – a global overview
- Planning, objectives, and direction
- Intelligence data collection
- Intelligence data processing
- Intelligence analysis and production
- Threat intelligence dissemination
- Threat intelligence feedback
Technical requirements
Cyber threat intelligence – a global overview
Characteristics of a threat
Threat intelligence and data security challenges
- The threat landscape: In most cases, cyberattacks are orchestrated by professionals and teams that have the necessary resources and training at their disposal. This includes state-sponsored attacks. However, with access to specific tools and training, private groups have developed sophisticated ways to conduct destructive cyberattacks. The landscape of threats is growing and changing as adversaries rely on new exploits and advanced social engineering techniques. McAfee Labs reported an average of 588 threats per minute (a 40% increase) in the third quarter of 2020, while Q3 to Q4 2020 saw more than a 100% increase in vulnerabilities and more than a 43% increase in malware.
- Security alerts and data growth: Organizations are acquiring different security platforms and technologies to address security concerns and challenges – sandbox, firewalls, incident response, threat hunting, fraud detection, intrusion detection, network scanners,...
Table of contents
- Mastering Cyber Intelligence
- Contributors
- Preface
- Section 1: Cyber Threat Intelligence Life Cycle, Requirements, and Tradecraft
- Chapter 1: Cyber Threat Intelligence Life Cycle
- Chapter 2: Requirements and Intelligence Team Implementation
- Chapter 3: Cyber Threat Intelligence Frameworks
- Chapter 4: Cyber Threat Intelligence Tradecraft and Standards
- Chapter 5: Goal Setting, Procedures for CTI Strategy, and Practical Use Cases
- Section 2: Cyber Threat Analytical Modeling and Defensive Mechanisms
- Chapter 6: Cyber Threat Modeling and Adversary Analysis
- Chapter 7: Threat Intelligence Data Sources
- Chapter 8: Effective Defense Tactics and Data Protection
- Chapter 9: AI Applications in Cyber Threat Analytics
- Chapter 10: Threat Modeling and Analysis – Practical Use Cases
- Section 3: Integrating Cyber Threat Intelligence Strategy to Business processes
- Chapter 11: Usable Security: Threat Intelligence as Part of the Process
- Chapter 12: SIEM Solutions and Intelligence-Driven SOCs
- Chapter 13: Threat Intelligence Metrics, Indicators of Compromise, and the Pyramid of Pain
- Chapter 14: Threat Intelligence Reporting and Dissemination
- Chapter 15: Threat Intelligence Sharing and Cyber Activity Attribution – Practical Use Cases
- Other Books You May Enjoy
Frequently asked questions
- Essential is ideal for learners and professionals who enjoy exploring a wide range of subjects. Access the Essential Library with 800,000+ trusted titles and best-sellers across business, personal growth, and the humanities. Includes unlimited reading time and Standard Read Aloud voice.
- Complete: Perfect for advanced learners and researchers needing full, unrestricted access. Unlock 1.4M+ books across hundreds of subjects, including academic and specialized titles. The Complete Plan also includes advanced features like Premium Read Aloud and Research Assistant.
Please note we cannot support devices running on iOS 13 and Android 7 or earlier. Learn more about using the app