A one-of-a-kind discussion of how to integrate cybersecurity into every facet of your organization
In See Yourself in Cyber: Security Careers Beyond Hacking, information security strategist and educator Ed Adams delivers a unique and insightful discussion of the many different ways the people in your organization—inhabiting a variety of roles not traditionally associated with cybersecurity—can contribute to improving its cybersecurity backbone. You'll discover how developers, DevOps professionals, managers, and others can strengthen your cybersecurity. You'll also find out how improving your firm's diversity and inclusion can have dramatically positive effects on your team's talent.
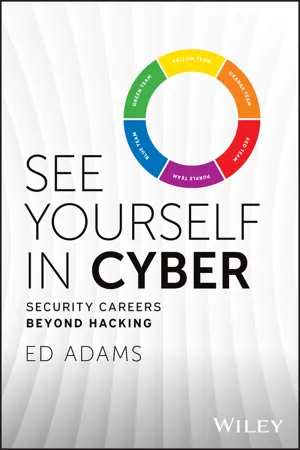
Using the familiar analogy of the color wheel, the author explains the modern roles and responsibilities of practitioners who operate within each "slice." He also includes:
- Real-world examples and case studies that demonstrate the application of the ideas discussed in the book
- Many interviews with established industry leaders in a variety of disciplines explaining what non-security professionals can do to improve cybersecurity
- Actionable strategies and specific methodologies for professionals working in several different fields interested in meeting their cybersecurity obligations
Perfect for managers, directors, executives, and other business leaders, See Yourself in Cyber: Security Careers Beyond Hacking is also an ideal resource for policymakers, regulators, and compliance professionals.