An easy to digest practical guide to Metasploit covering all aspects of the framework from installation, configuration, and vulnerability hunting to advanced client side attacks and anti-forensics.About This Book• Carry out penetration testing in highly-secured environments with Metasploit• Learn to bypass different defenses to gain access into different systems.• A step-by-step guide that will quickly enhance your penetration testing skills. Who This Book Is ForIf you are a penetration tester, ethical hacker, or security consultant who wants to quickly learn the Metasploit framework to carry out elementary penetration testing in highly secured environments then, this book is for you.What You Will Learn• Get to know the absolute basics of the Metasploit framework so you have a strong foundation for advanced attacks• Integrate and use various supporting tools to make Metasploit even more powerful and precise• Set up the Metasploit environment along with your own virtual testing lab• Use Metasploit for information gathering and enumeration before planning the blueprint for the attack on the target system• Get your hands dirty by firing up Metasploit in your own virtual lab and hunt down real vulnerabilities• Discover the clever features of the Metasploit framework for launching sophisticated and deceptive client-side attacks that bypass the perimeter security• Leverage Metasploit capabilities to perform Web application security scanningIn DetailThis book will begin by introducing you to Metasploit and its functionality. Next, you will learn how to set up and configure Metasploit on various platforms to create a virtual test environment. You will also get your hands on various tools and components used by Metasploit.Further on in the book, you will learn how to find weaknesses in the target system and hunt for vulnerabilities using Metasploit and its supporting tools. Next, you'll get hands-on experience carrying out client-side attacks. Moving on, you'll learn about web application security scanning and bypassing anti-virus and clearing traces on the target system post compromise. This book will also keep you updated with the latest security techniques and methods that can be directly applied to scan, test, hack, and secure networks and systems with Metasploit.By the end of this book, you'll get the hang of bypassing different defenses, after which you'll learn how hackers use the network to gain access into different systems.Style and approachThis tutorial is packed with step-by-step instructions that are useful for those getting started with Metasploit. This is an easy-to-read guide to learning Metasploit from scratch that explains simply and clearly all you need to know to use this essential IT power tool.
- 190 pages
- English
- ePUB (mobile friendly)
- Available on iOS & Android
eBook - ePub
Metasploit for Beginners
About this book
Trusted by 375,005 students
Access to over 1 million titles for a fair monthly price.
Study more efficiently using our study tools.
Information
Information Gathering with Metasploit
Information gathering and enumeration are the initial stages of penetration testing life cycle. These stages are often overlooked, and people directly end up using automated tools in an attempt to quickly compromise the target. However, such attempts are less likely to succeed.
"Give me six hours to chop down a tree and I will spend the first four sharpening the axe."
- Abraham Lincoln
- Abraham Lincoln
This is a very famous quote by Abraham Lincoln which is applicable to penetration testing as well! The more efforts you take to gather information about your targets and enumerate them, the more likely you are to succeed with compromise. By performing comprehensive information gathering and enumeration, you will be presented with wealth of information about your target, and then you can precisely decide the attack vector in order to compromise the same.
The Metasploit Framework provides various auxiliary modules for performing both passive and active information gathering along with detailed enumeration. This chapter introduces some of the important information gathering and enumeration modules available in the Metasploit Framework:
The topics to be covered are as follows:
- Information gathering and enumeration on various protocols
- Password sniffing with Metasploit
- Advanced search using Shodan
Information gathering and enumeration
In this section, we'll explore various auxiliary modules within the Metasploit Framework that can be effectively used for information gathering and enumeration of various protocols such as TCP, UDP, FTP, SMB, SMTP, HTTP, SSH, DNS, and RDP. For each of these protocols, you will learn multiple auxiliary modules along with the necessary variable configurations.
Transmission Control Protocol
Transmission Control Protocol (TCP) is a connection-oriented protocol and ensures reliable packet transmission. Many of the services such as Telnet, SSH, FTP, and SMTP make use of the TCP protocol. This module performs a simple port scan against the target system and tells us which TCP ports are open.
Its auxiliary module name is auxiliary/scanner/portscan/tcp, and you will have to configure the following parameters:
- RHOSTS: IP address or IP range of the target to be scanned
- PORTS: Range of ports to be scanned
We can see this auxiliary module in the following screenshot:

User Datagram Protocol
User Datagram Protocol (UDP) is lightweight compared to TCP, however, not as reliable as TCP. UDP is used by services such as SNMP and DNS. This module performs a simple port scan against the target system and tells us which UDP ports are open.
Its auxiliary module name is auxiliary/scanner/discovery/udp_sweep, and you will have to configure the following parameters:
- RHOSTS: IP address or IP range of the target to be scanned
We can see this auxiliary module in the following screenshot:

File Transfer Protocol
File Transfer Protocol (FTP) is most commonly used for file sharing between the client and server. FTP uses TCP port 21 for communication.
Let's go through some of the following FTP auxiliaries:
- ftp_login: This module helps us perform a brute-force attack against the target FTP server.
Its auxiliary module name is auxiliary/scanner/ftp/ftp_login, and you will have to configure the following parameters:
-
- RHOSTS: IP address or IP range of the target to be scanned
- USERPASS_FILE: Path to the file containing the username/password list
You can either create your own custom list that can be used for a brute-force attack, or there are many wordlists instantly available for use in Kali Linux, located at |usr|share|wordlists.
We can see this auxiliary module in the following screenshot:

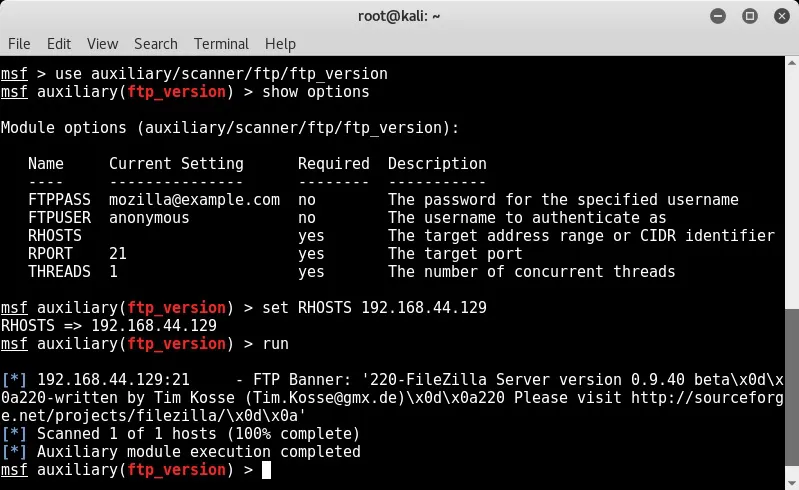
- ftp_version: This module uses the banner grabbing technique to detect the version of the target FTP server.
Its auxiliary module name is auxiliary/scanner/ftp/ftp_version, and you will have to configure the following parameters:
- RHOSTS: IP address or IP range of the target to be scanned
Once you know the version of the target service, you can start searching for version specific vulnerabilities and corresponding exploits.
We can see this auxiliary module in the following screenshot:
- anonymous: Some FTP servers are misconfigured in a way that they allow anonymous access to remote users. This auxiliary module probes the target FTP server to check whether it allows anonymous access.
Its auxiliary module name is ...
Table of contents
- Title Page
- Copyright
- Credits
- About the Author
- About the Reviewer
- www.PacktPub.com
- Customer Feedback
- Preface
- Introduction to Metasploit and Supporting Tools
- Setting up Your Environment
- Metasploit Components and Environment Configuration
- Information Gathering with Metasploit
- Vulnerability Hunting with Metasploit
- Client-side Attacks with Metasploit
- Web Application Scanning with Metasploit
- Antivirus Evasion and Anti-Forensics
- Cyber Attack Management with Armitage
- Extending Metasploit and Exploit Development
Frequently asked questions
Yes, you can cancel anytime from the Subscription tab in your account settings on the Perlego website. Your subscription will stay active until the end of your current billing period. Learn how to cancel your subscription
No, books cannot be downloaded as external files, such as PDFs, for use outside of Perlego. However, you can download books within the Perlego app for offline reading on mobile or tablet. Learn how to download books offline
Perlego offers two plans: Essential and Complete
- Essential is ideal for learners and professionals who enjoy exploring a wide range of subjects. Access the Essential Library with 800,000+ trusted titles and best-sellers across business, personal growth, and the humanities. Includes unlimited reading time and Standard Read Aloud voice.
- Complete: Perfect for advanced learners and researchers needing full, unrestricted access. Unlock 1.4M+ books across hundreds of subjects, including academic and specialized titles. The Complete Plan also includes advanced features like Premium Read Aloud and Research Assistant.
We are an online textbook subscription service, where you can get access to an entire online library for less than the price of a single book per month. With over 1 million books across 990+ topics, we’ve got you covered! Learn about our mission
Look out for the read-aloud symbol on your next book to see if you can listen to it. The read-aloud tool reads text aloud for you, highlighting the text as it is being read. You can pause it, speed it up and slow it down. Learn more about Read Aloud
Yes! You can use the Perlego app on both iOS and Android devices to read anytime, anywhere — even offline. Perfect for commutes or when you’re on the go.
Please note we cannot support devices running on iOS 13 and Android 7 or earlier. Learn more about using the app
Please note we cannot support devices running on iOS 13 and Android 7 or earlier. Learn more about using the app
Yes, you can access Metasploit for Beginners by Sagar Rahalkar in PDF and/or ePUB format, as well as other popular books in Computer Science & Cyber Security. We have over one million books available in our catalogue for you to explore.