- 101 pages
- English
- PDF
- Available on iOS & Android
eBook - PDF
Information Security based on ISO 27001/ISO 27002
About this book
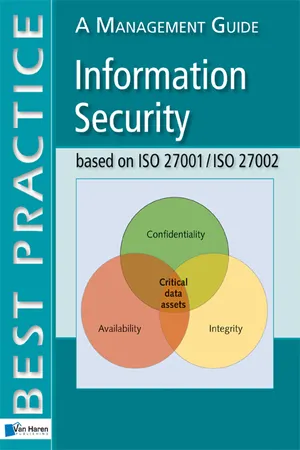
Information is the currency of the information age and in many cases is the most valuable asset possessed by an organisation. Information security management is the discipline that focuses on protecting and securing these assets against the threats of natural disasters, fraud and other criminal activity, user error and system failure.
This Management Guide provides an overview of the two international information security standards, ISO/IEC 27001 and ISO 27002. These standards provide a basis for implementing information security controls to meet an organisation's own business requirements as well as a set of controls for business relationships with other parties.
This Guide provides:
An introduction and overview to both the standards
The background to the current version of the standards
Links to other standards, such as ISO 9001, BS25999 and ISO 20000
Links to frameworks such as CobiT and ITIL
Above all, this handy book describes how ISO 27001 and ISO 27002 interact to guide organizations in the development of best practice information security management systems.
Trusted by 375,005 students
Access to over 1.5 million titles for a fair monthly price.
Study more efficiently using our study tools.
Information
Topic
EducationSubtopic
Business DevelopmentTable of contents
- 1 Introduction
- 2 Information security
- 3 Background to the Standards
- 4 Relationship between the Standards
- 5 Use of the Standards
- 6 Certification process and
- 7 Overview of ISO 27001
- 8 Summary of changes from
- 9 Overview of ISO 27002:2005
- 10 Summary of changes from ISO 27002:2000
- 11 ISO 27000 series in future
- 12 Compatibility and integration with other management systems
- 13 Documentation requirements and record control
- 14 Management responsibility
- 15 Process approach and the PDCA cycle
- 16 Scope definition
- 17 Policy definition
- 18 Risk assessment
- 19 Risk treatment plan
- 20 The Statement of Applicability
- 21 Do - implement and operate the ISMS
- 22 Check - monitor and review the ISMS
- 23 Act - maintain and improve the ISMS
- 24 ISO 27001:2005 Annex A
- 25 Annex A control areas and controls
- 26 ISO 27001 and CobiT
- 27 ISO 27001, ITIL and ISO 20000
- Appendix A Bibliography of related standards and guides
- Appendix B Accredited certification and other bodies
Frequently asked questions
Yes, you can cancel anytime from the Subscription tab in your account settings on the Perlego website. Your subscription will stay active until the end of your current billing period. Learn how to cancel your subscription
No, books cannot be downloaded as external files, such as PDFs, for use outside of Perlego. However, you can download books within the Perlego app for offline reading on mobile or tablet. Learn how to download books offline
Perlego offers two plans: Essential and Complete
- Essential is ideal for learners and professionals who enjoy exploring a wide range of subjects. Access the Essential Library with 800,000+ trusted titles and best-sellers across business, personal growth, and the humanities. Includes unlimited reading time and Standard Read Aloud voice.
- Complete: Perfect for advanced learners and researchers needing full, unrestricted access. Unlock 1.5M+ books across hundreds of subjects, including academic and specialized titles. The Complete Plan also includes advanced features like Premium Read Aloud and Research Assistant.
We are an online textbook subscription service, where you can get access to an entire online library for less than the price of a single book per month. With over 1.5 million books across 990+ topics, we’ve got you covered! Learn about our mission
Look out for the read-aloud symbol on your next book to see if you can listen to it. The read-aloud tool reads text aloud for you, highlighting the text as it is being read. You can pause it, speed it up and slow it down. Learn more about Read Aloud
Yes! You can use the Perlego app on both iOS and Android devices to read anytime, anywhere — even offline. Perfect for commutes or when you’re on the go.
Please note we cannot support devices running on iOS 13 and Android 7 or earlier. Learn more about using the app
Please note we cannot support devices running on iOS 13 and Android 7 or earlier. Learn more about using the app
Yes, you can access Information Security based on ISO 27001/ISO 27002 by Alan Calder in PDF and/or ePUB format, as well as other popular books in Education & Business Development. We have over 1.5 million books available in our catalogue for you to explore.