![]()
1
THE AUTHENTIC SERVICE PROGRESSION (TASP)
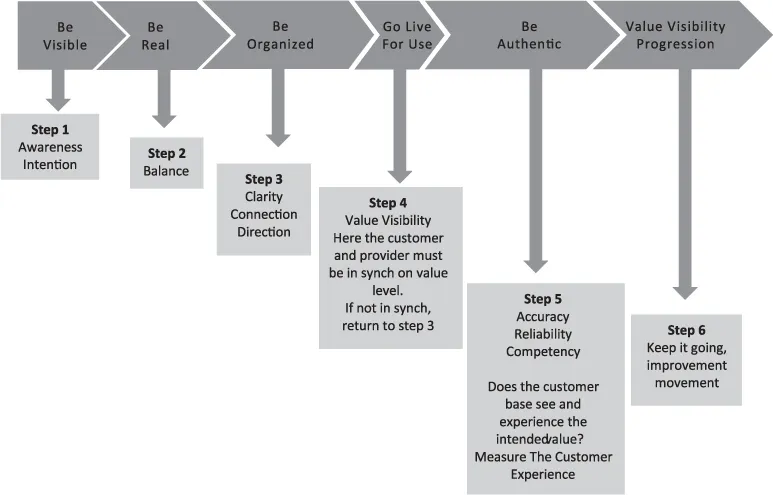
The Authentic Service Progression is derived from IT Service Management (ITSM) successes using formal frameworks and practical approaches. The Authentic Service Progression (TASP) is a unified workflow, which produces value visibility. It does this by delivering technology services in accordance with business investment and authenticity. Matching cost to quality is significant to setting the right customer expectation. There are gaps that need attention between service performance and cost investment.
To address some gaps, managers may apply quick remedies to accommodate for them. It’s a dangerous practice when technical managers begin to make up allowances for shortages between investment and service. In the moment it makes the customer temporarily happy; however, in hindsight, the long-term effects damage the integrity of the provider. In this scenario, make ups cannot be sustained long term and then end up costing more, damaging the provider’s reputation, and customer relationship. This scenario misleads a customer’s expectations with an impossible set of promises the provider isn’t able to meet. When a provider’s reputation is tarnished, in the customers view they aren’t trustworthy. Customer relationships must be built on open and direct communication. The IT unit needs to be dependable and upright so when there is conflict or a crisis, the customer has confidence in the provider’s capabilities. When implementing an authentic service progression model, value naturally happens. In a process producing value, the customer gains assurance on the provider’s integrity. TASP is Practical ITSM.
Practical ITSM indicates a union of people and technology and it has four limbs: People, Progression, Business, and Technology.
The first limb, People, deals with business culture, etiquette, self-discipline, focusing on our behavior, how we conduct ourselves in business and improvement.
The second limb, Progression, deals with connectedness, balance, making good use of the businesses competencies, forming team alliance, developing effective habits for business maturity, observing habits to recognize those negatively impacting business intentions, and improvement.
The third limb, Business deals with purpose, portfolio of products and services, finance, functions, energetic business awareness, which prepares staff for change, distribution, and improvement.
The fourth limb, Technology, deals with automation, an uninterrupted flow of power-driven energy, a means to deliver, record, store, produce, replicate, recognizing nothing is picture perfect and not giving up, and improvement.
The four limbs are to help businesses mature with ITSM and overcome challenges stemming from a lack of planning or ineffective ITSM implementations. The four limbs are linked by the value process flow (Fig. 7).
A business culture that demonstrates adaptability and places a high level of importance on customers is necessary to carry out a value process flow (Fig. 1). The output of a value process flow is value visibility to consumers. The primary intention is to enable IT units to present as a unified business. One way to establish this is by positioning technology units as a strategic force in the business. Position IT in the same manner as a sales department (Chapter 1: Positioning IT as a Sales Organization). Doing so promotes an authentic image and relationship with customers.
People in business are linked through technology. Technology can accelerate the interconnectedness of a business, but is the organization as connected, as it should be? Being connected through technology is a double-edged sword and the varying extremes of people’s understanding and ineffective communication can wear away the ties of being connected. Often, you hear about opposite views and opinions on technology and communication. There is one side that feels modern platforms are like resident evil replacing people resources and diminishing human-to-human relationships. On the other side, people think modern platforms are interconnecting humans faster and better on a universal level. The digital age of data and knowledge enhances communication and both sides have valid points. Both sides balanced accurately provide a modern platform for useful communication and information.
Service management outdates its usefulness quickly when focused entirely on technology.
Exercising useful communication through modern platforms is almost as successful as surfing during low tide. Why? Because messages are ambiguous, receivers are likely to clarify messages for themselves in non-conforming ways and resonate only with what matches their expectations. For example, if two people are involved in an escalation and one party assumes that the other is going to be aggressive or hostile, then any message received from them will be interpreted as aggressive and hostile.
Our expectations are like blinders or filters that most likely will distort what we see and read. For example, electronic messages about a service escalation are interpreted to fit our preconceived perception on what we know about the situation. Any new information we learn through messaging is compared with the knowledge we already have. To accurately interpret electronic messages depends upon the factual and current knowledge accessible about the escalation. If not, then our previous assumptions or interpretation of the situation may get distorted in our mind and crafted to fit our view on what’s happening.
Perception fosters assumptions and may dismiss important information entirely.
The essential point: useful and good communication is a result of being on the same wavelength between messenger and receiver. To be on the same wavelength requires a blend of electronic messaging and verbal communication. Verbal communication is used to get everyone involved in the escalation on the same wavelength. Verbal messaging is used to set accurate expectation. Electronic messaging should be in line with what is verbally and mutually agreed upon.
During verbal interactions, identify and understand each party’s perception.
Collect and store information that is factual and arrange electronic communication schedules.
To be on the same wavelength also implies all aspects of the business are connected and understood. When it comes to interpretation, this is an area where ITSM is like a sinkhole. The concepts and techniques in ITSM frameworks are easy to understand but making sense of them to use in real-world situations is much different than understanding them in a training environment. To make sense of theory, teams need to be on the same wavelength about conceptual theories and how the organization uses them. Mutual understanding and interpretation on practices, policies, concepts, theories, and goals must be part of the core ITSM model.
Misunderstanding is the distance that keeps people separated.
Tips for fostering mutual understanding:
Ensure all business staff shares the same vision and has good understanding of each other’s role in that vision. Cultivate a business culture that is cohesive and responsive.
– For example, a financial company wanted to customize a service component for one of its major customers. Doing so required extensive design reconfiguration, with changes to hosting, transition to cloud computing, pricing, and service delivery. Although every function agreed to take on these changes that affected their teams, they all worked on them independently and within different time frames. What each function didn’t realize was that their part was triggered by different departments. This created a continual cycle of design changes. As a consequence, the company was unable to finalize a solid integrated design. They couldn’t provide a firm quote to the customer and a delivery schedule expanded from one to two years.
Get involved in each other’s departments activities....