Fraud Data Analytics Methodology addresses the need for clear, reliable fraud detection with a solid framework for a robust data analytic plan. By combining fraud risk assessment and fraud data analytics, you'll be able to better identify and respond to the risk of fraud in your audits. Proven techniques help you identify signs of fraud hidden deep within company databases, and strategic guidance demonstrates how to build data interrogation search routines into your fraud risk assessment to locate red flags and fraudulent transactions. These methodologies require no advanced software skills, and are easily implemented and integrated into any existing audit program. Professional standards now require all audits to include data analytics, and this informative guide shows you how to leverage this critical tool for recognizing fraud in today's core business systems.
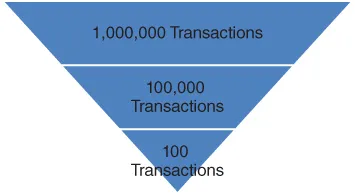
Fraud cannot be detected through audit unless the sample contains a fraudulent transaction. This book explores methodologies that allow you to locate transactions that should undergo audit testing.
- Locate hidden signs of fraud
- Build a holistic fraud data analytic plan
- Identify red flags that lead to fraudulent transactions
- Build efficient data interrogation into your audit plan
Incorporating data analytics into your audit program is not about reinventing the wheel. A good auditor must make use of every tool available, and recent advances in analytics have made it accessible to everyone, at any level of IT proficiency. When the old methods are no longer sufficient, new tools are often the boost that brings exceptional results. Fraud Data Analytics Methodology gets you up to speed, with a brand new tool box for fraud detection.