
CompTIA PenTest+ Study Guide
Exam PT0-002
Mike Chapple, David Seidl
- English
- ePUB (apto para móviles)
- Disponible en iOS y Android
CompTIA PenTest+ Study Guide
Exam PT0-002
Mike Chapple, David Seidl
Información del libro
Prepare for success on the new PenTest+ certification examand an exciting career in penetration testing
In therevamped Second Edition of CompTIA PenTest+ Study Guide: Exam PT0-002, veteran information security expertsDr.Mike Chapple and David Seidl delivera comprehensiveroadmap to the foundational and advanced skills everypentester(penetration tester)needs tosecure their CompTIAPenTest+ certification, ace their next interview, and succeed in an exciting new career in a growing field.
You'lllearn toperformsecurityassessments of traditional servers, desktopand mobileoperating systems, cloudinstallations, Internet-of-Thingsdevices, and industrial or embedded systems.You'llplan and scope a penetration testing engagement including vulnerability scanning, understand legal andregulatorycompliance requirements, analyzetestresults, and produce a written report with remediation techniques.
This book will:
- Prepareyoufor success on thenewly introduced CompTIA PenTest+ PT0-002 Exam
- Multiply your career opportunities witha certification that complies with ISO 17024standards and meetsDepartment of DefenseDirective 8140/8570.01-M requirements
- Allow accesstothe Sybex online learning center, with chapter review questions, full-length practice exams, hundreds of electronic flashcards, and a glossary of key terms
Perfect for anyonepreparingfor the updated CompTIA PenTest+ certification exam, CompTIA PenTest+ Study Guide: Exam PT0-002 is also a must-read resource foraspiring penetration testers and IT security professionals seeking to expand and improve their skillset.
Preguntas frecuentes
Información
Chapter 1
Penetration Testing
- 1.3 Given a scenario, demonstrate an ethical hacking mindset by maintaining professionalism and integrity.
- Background checks of penetration testing team
- Adhere to specific scope of engagement
- Identify criminal activity
- Immediately report breaches/criminal activity
- Limit the use of tools to a particular engagement
- Limit invasiveness based on scope
- Maintain confidentiality of data/information
- Risks to the professional
What Is Penetration Testing?
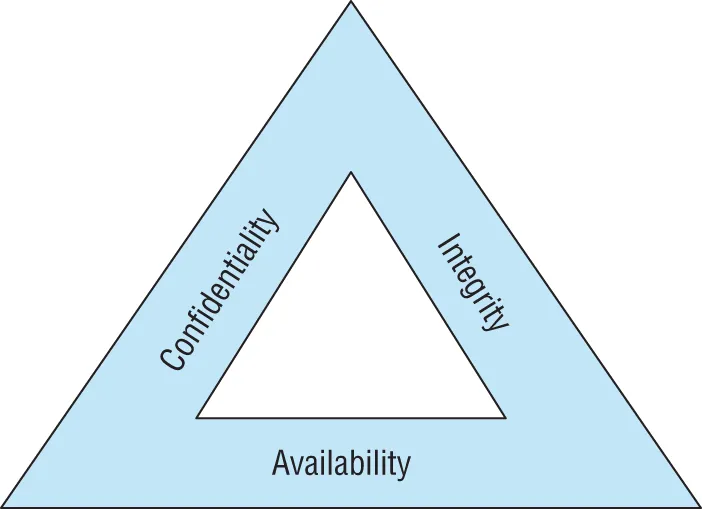
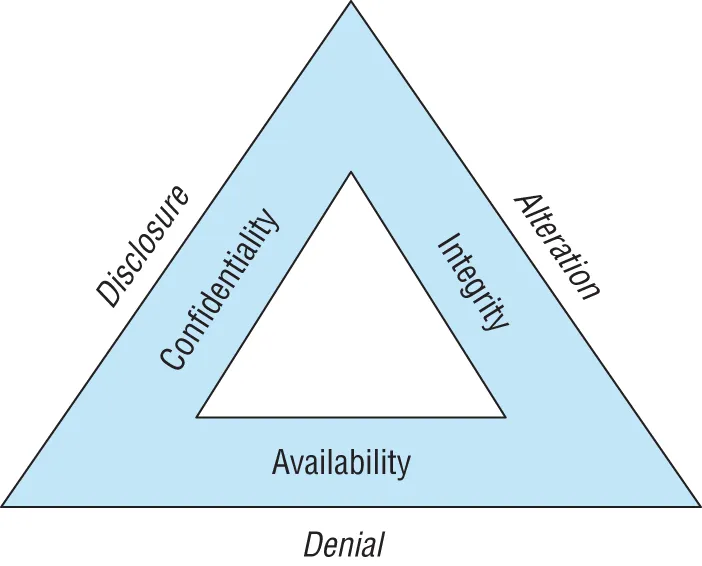
Cybersecurity Goals
- Confidentiality measures seek to prevent unauthorized access to information or systems.
- Integrity measures seek to prevent unauthorized modification of information or systems.
- Availability measures seek to ensure that legitimate use of information and systems remains possible.
- Disclosure attacks seek to gain unauthorized access to information or systems.
- Alteration attacks seek to make unauthorized changes to information or systems.
- Denial attacks seek to prevent legitimate use of information and systems.
Adopting the Hacker Mindset
- Security cameras in high‐risk areas
- Auditing of cash register receipts
- Theft detectors at the main entrance/exit of the store
- Exit alarms on emergency exits
- Burglar al...