![]()
CHAPTER ONE
Why No Organization Is Immune to Fraud
Did you know that:
• Organizations lose an average of 7 percent of gross revenue to fraud every year? In 2008 that represented approximately $994 billion.1
• The most common method by which fraud is detected is tips? Over 46 percent of cases that are detected are reported via a tip from an employee, vendor, or other whistle-blower.2
• Fraudulent financial reporting—the main form of management fraud, is twice as common in organizations as billing schemes—the most common form of employee-level fraud?3
• Organizations that implement entity-wide fraud awareness training cut fraud losses by 52 percent?4
• Seventy-four percent of employees report that they have observed or have firsthand knowledge of wrongdoing in their organization in the past 12 months?5
• The average fraudulent financial reporting fraud costs the victim organization $2 million, while the average loss per incident of billing fraud is only $100,000?6
• The majority of public companies investigated by the Securities and Exchange Commission (SEC) for fraud subsequently suffer a substantial decline in stock price (50 percent or more)?7
• It takes an average of 24 months for a fraud to be detected?8
• One-third of large-organization executives say they have no documented investigative policies or procedures for fraud, and one-half have no incident response plan?9
• One-quarter of companies consider themselves highly vulnerable to information theft, and 29 percent have experienced information theft, loss, or attack in the past three years?10
• The most common type of fraud affecting institutions, by far, is theft of assets—which can include money, services, or physical assets?11
Chapter 1 introduces the critical notion that you as a financial professional have considerable power to prevent, detect, and report fraud. The chapter also covers the following topics:
• The multiple definitions of fraud that make it critical to clarify the real meaning of the term in your mind
• A number of widespread myths about fraud and the realities that they misinterpret
• Management’s role as the standard setter for an ethical and law-abiding institutional culture
It is not possible to compile a workbook on fraud fighting without relying to a considerable degree on the prodigious and wide-ranging research conducted by the Association of Certified Fraud Examiners (ACFE). However, in addition to this authoritative body, founded in 1988 in Austin, Texas, by Joseph T. Wells, the Big Daddy of the anti-fraud profession, there are other respected institutions whose research provides additional useful material for the study of institutional fraud.
As with the list of statistics that open the chapter, the following pages draw on key findings of numerous prominent consulting, research, and academic institutions that are active in supporting the fight against fraud in organizations of all kinds—corporations, both public and private, not-for-profit organizations, and governmental agencies. These carefully selected statistics provide a framework defining the vast scope of the fraud problem. With the perspective provided by these data, you will be equipped with a solid understanding of the magnitude of the fraud problem, along with key trends and patterns in major categories of fraud.
What Is Fraud?
Most people involved in the fraud-fighting business have their own concept of what fraud is—and what it isn’t. As a result we have a grab bag of definitions to choose from in guiding our day-to-day work. Some are legal definitions. Others are academic, while still others are based on personal experience. Out of the lot, the most useful definitions boil down to two.
According to the ACFE, fraud is:
Any illegal acts characterized by deceit, concealment, or violation of trust. These acts are not dependent upon the application of threat of violence or of physical force. Frauds are perpetrated by individuals and organizations to obtain money, property, or services; to avoid payment or loss of services; or to secure personal or business advantage.12
According to the American Institute of Certified Public Accountants (AICPA), fraud is:
A broad legal concept that is distinguished from error depending on whether the action is intentional or unintentional.13
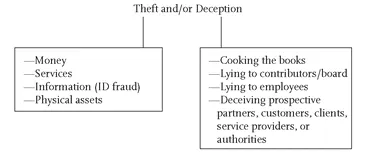
Exhibit 1.1 White-Collar Crime 101 Definition
The bottom line. Regardless of whose definition of fraud you accept, you will find that nearly all incidents of fraudulent activity—also called white-collar crime—fall into one or both of two categories: Theft and Deception. Exhibit 1.1 is a graphic illustration of this dual-category definition of fraud, as formulated by White-Collar Crime 101.
Myths and Realities about Fraud
One of the key reasons for the astounding breadth and depth of the fraud problem is that management often operates under the false impression that its organization is immune to fraud.
More precisely, top executives like to think that because they have complied with rules and laws requiring them to put internal controls in place, they are adequately protected against attacks by white-collar criminals. In reality, no organization—no matter how well-designed its internal controls against fraud are—can ever be fully protected against determined fraudsters. The bad guys always find loopholes or weaknesses in your operations that they can exploit to steal cash, forge checks, collude with vendors, falsify financial reports, steal confidential data, or commit any of a million other crimes that cause either financial or reputational damage—or both.
In addition to this false sense of self-protection, other common yet potentially costly misconceptions that senior managers often have about fraud are illustrated in the following myths.
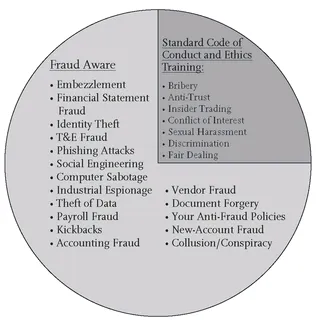
• Myth #1: Ethics and Compliance Training “Has Us Covered”
This myth assumes that such training addresses key issues about fraud and instructs employees how to detect the red flags of fraud and how to report it. See Exhibit 1.2.
In fact, compliance and ethics typically have little to do with fraud. Nearly all organizations have a code of ethics on which this training is based. However the vast majority of such codes don’t even contain the word “fraud.”
In most organizations, such a code informs employees about issues like sexual harassment, antitrust issues, accepting gifts from vendors, and other ethical matters that are important—but are not related to fraud.
The important thing to remember is that while all fraud is unethical, not all unethical conduct is fraudulent. For example, accepting a generous gift from a vendor—such as a free vacation, tickets to professional sporting events, or other such items—is unethical and most likely in direct violation of your organization’s ethics policy. However, such gifts are not necessarily illegal, and hence they often do not represent fraud.
Exhibit 1.2 Fraud Training versus Ethics Training
• Myth #2: Our Finance Staff Are Qualified to Protect Us Against Fraud
This notion is equally misconceived. Internal auditors, financial managers, accountants, treasurers, and other professionals in most organizations are usually untrained in fraud detection and prevention, and they most certainly are not trained—let alone expected—to be fraud investigators. However, in many organizations, there is growing pressure for internal auditors and other financial managers to focus more on fraud detection—which may be one reason you are reading this book!
• Myth #3: We Have Very Little Fraud Here
The problem arises when this assumption is made without firm quantitative proof. In too...