Homeland Security
An Introduction to Principles and Practice
Charles P. Nemeth
- 592 pages
- English
- ePUB (adapté aux mobiles)
- Disponible sur iOS et Android
Homeland Security
An Introduction to Principles and Practice
Charles P. Nemeth
À propos de ce livre
Homeland Security: An Introduction to Principles and Practice, Fourth Edition continues its record of providing a fully updated, no-nonsense textbook to reflect the latest policy, operational, and program changes to the Department of Homeland Security (DHS) over the last several years. The blend of theory with practical application instructs students on how to understand the need to reconcile policy and operational philosophy with the real-world use of technologies and implementation of practices.
The new edition is completely updated to reflect changes to both new challenges and continually changing considerations. This includes facial recognition, intelligence gathering techniques, information sharing databases, white supremacy, domestic terrorism and lone wolf actors, border security and immigration, the use of drones and surveillance technology, cybersecurity, the status of ISIS and Al Qaeda, the increased nuclear threat, COVID-19, ICE, DACA, and immigration policy challenges. Consideration of, and the coordinated response, to all these and more is housed among a myriad of federal agencies and departments.
Features
• Provides the latest organizational changes, restructures, and policy developments in DHS
• Outlines the role of multi-jurisdictional agencies—this includes stakeholders at all levels of government relative to the various intelligence community, law enforcement, emergency managers, and private sector agencies
• Presents a balanced approach to the challenges the federal and state government agencies are faced with in emergency planning and preparedness, countering terrorism, and critical infrastructure protection
• Includes full regulatory and oversight legislation passed since the last edition, as well as updates on the global terrorism landscape and prominent terrorist incidents, both domestic and international
• Highlights emerging, oftentimes controversial, topics such as the use of drones, border security and immigration, surveillance technologies, and pandemic planning and response
• Contains extensive pedagogy including learning objectives, sidebar boxes, chapter summaries, end of chapter questions, Web links, and references for ease in comprehension
Homeland Security, Fourth Edition continues to serve as the comprehensive and authoritative text on homeland secuirty. The book presents the various DHS state and federal agencies and entities within the government—their role, how they operate, their structure, and how they interact with other agencies—to protect U.S. domestic interests from various dynamic threats.
Ancillaries including an Instructor's Manual with Test Bank and chapter PowerPointTM slides for classroom presentation are also available for this book and can be provided for qualified course instructors.
Charles P. Nemeth
is a recognized expert in homeland security and a leader in the private security industry, private sector justice, and homeland security education. He has more than 45 book publications and is currently Chair of the Department of Security, Fire, and Emergency Management at John Jay College in New York City.
Foire aux questions
Informations
1 The Idea and Origin of Homeland Security
OBJECTIVES
- To identify major twentieth- and twenty-first-century events, both domestic and international, that formed the United States’ current policy position on homeland security
- To comprehend that war, by its very nature, its military tactics and strategies, and governmental policies, relies on forms of terror to meet its goals
- To analyze the effect the Cold War had on shaping Americans’ notions of terror and to understand the evolution of the government’s policy responses
- To describe the domestic events of the turbulent 1960s and 1970s to shed light on the country’s response to domestic terrorism as well as gain an understanding of the unique motivations of the domestic terrorist
- To differentiate the motives of the international terrorist from the domestic terrorist and comprehend that although the methods may be the same, the motivations differ
- To explain the unique motivations of the jihadist by exploring attacks against U.S. military targets and discover the motivations leading up to the events of 9/11
- To evaluate specific international terror incidents against U.S. installations prior to 9/11 to gain an understanding of the jihadist mentality that led up to the terror attacks against the Twin Towers and the Pentagon
- To identify specific domestic terror attacks, such as those perpetuated by Timothy McVeigh and Ted Kaczynski, the Tree of Life-Pittsburgh Synagogue Shooter, by way of examples, in light of the effect these types of attacks have on national security policy
1.1 Introduction
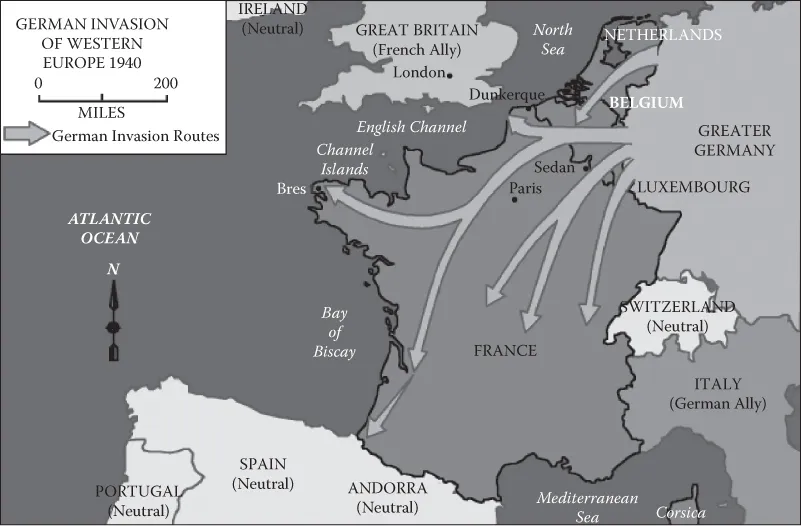
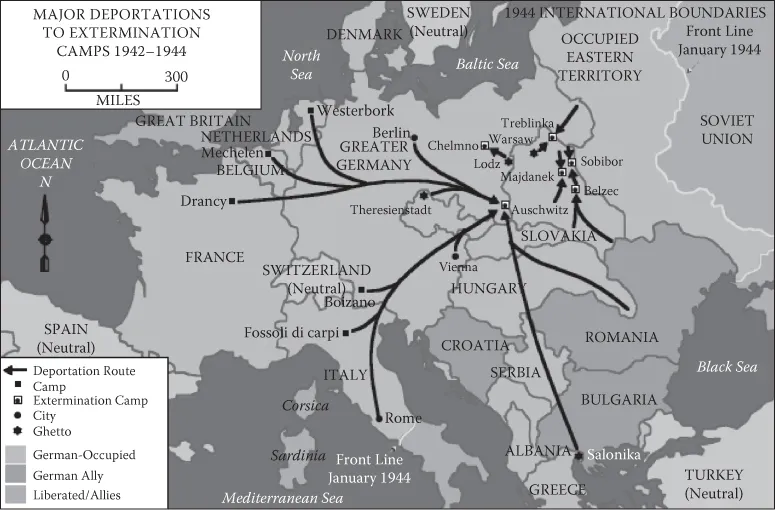
1.2 Threats to the Homeland: Twentieth-Century Military Movements