Introduction to the Cyber Ranges
Bishwajeet Pandey, Shabeer Ahmad
- 176 pages
- English
- ePUB (adapté aux mobiles)
- Disponible sur iOS et Android
Introduction to the Cyber Ranges
Bishwajeet Pandey, Shabeer Ahmad
À propos de ce livre
Introduction to the Cyber Ranges provides a comprehensive, integrative, easy-to-comprehend overview of different aspects involved in the cybersecurity arena. It expands on various concepts like cyber situational awareness, simulation and emulation environments, and cybersecurity exercises. It also focuses on detailed analysis and the comparison of various existing cyber ranges in military, academic, and commercial sectors. It highlights every crucial aspect necessary for developing a deeper insight about the working of the cyber ranges, their architectural design, and their need in the market. It conveys how cyber ranges are complex and effective tools in dealing with advanced cyber threats and attacks.
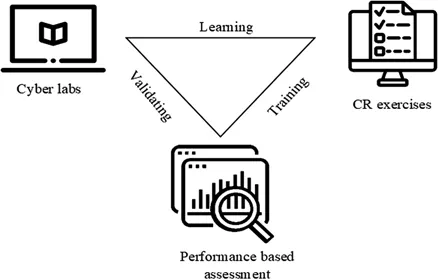
Enhancing the network defenses, resilience, and efficiency of different components of critical infrastructures is the principal objective of cyber ranges. Cyber ranges provide simulations of possible cyberattacks and training on how to thwart such attacks. They are widely used in urban enterprise sectors because they present a sturdy and secure setting for hands-on cyber skills training, advanced cybersecurity education, security testing/training, and certification.
Features:
-
- A comprehensive guide to understanding the complexities involved with cyber ranges and other cybersecurity aspects
-
- Substantial theoretical knowhow on cyber ranges, their architectural design, along with case studies of existing cyber ranges in leading urban sectors like military, academic, and commercial
-
- Elucidates the defensive technologies used by various cyber ranges in enhancing the security setups of private and government organizations
-
- Information organized in an accessible format for students (in engineering, computer science, and information management), professionals, researchers, and scientists working in the fields of IT, cybersecurity, distributed systems, and computer networks
Foire aux questions
Informations
1Introduction
1.1 CSA
- Perception encompasses the awareness of the individual's own locus concerning the setting of additional entities and environmental factors.
- Comprehension of the causes, impacts, and consequences of the external influences to the systems with analyzing the changes in the situations/surroundings over time.
- Projection or predictions of the likely developments from the existing to approaching situation.
- Resolution includes the recovery and repair of the damage caused to the system.
- Managing e-commercial enterprisesNowadays, a lot of transactions on e-commerce websites (like eBay and Amazon) are being processed on daily basis. For smooth flow of business, it is crucial to monitor and analyze all kinds of possible cyber threats and the vulnerabilities in the cyber infrastructure and components.
- GSA
GSA monitor millions of a country's citizens’ assets, national critical infrastructures, as they are accountable for protecting the citizens within the country as well as overseas. The security of the database containing every citizen's record should not be compromised.
- Network components such as
IDs, firewalls, monitoring systems, and scanners collect the data, report alerts, and generate logs. Security operator/team uses this data to perceive the situation and keep track of potential cyber threats. - Next, the security operator/team uses technology and processes to combine, evaluate, integrate, and compare the perceived data to comprehend the current situation and update the knowledge-base as well.
- After this step, based on the data perceived and comprehended, the security operator/team can now put forth accurate predictions of the patterns of cyberattacks. They can now answer the questions like, what kind of cyber scenarios are probable, what are the feasible methods by which the current susceptibilities can be manipulated or worsened, and what measures can be implemented?
- Lastly, the security operator/team is able to propose and employ the required sequence of action and countermeasure controls for resolving in-built risks or cyberattacks in cybernetworks.
- Data source: the CSA system can be used for generating complete and high-quality data. This ensures the authenticity of the data for other users, stakeholders, and other systems.
- Assets organization and interconnectivity: the system is a common platform for assets sharing and organizing. Organizing assets and their dependencies and associations makes them easily identifiable by the users. They can be shared between the physical and the logical units of the network. New components and CSA scenarios can also be developed from the knowledge and usage of preexisting assets of the network.
- Assessing risks: situation comprehension and projection, both can be achieved by assessing the potential impact of a network threat scenarios. This assessment can be performed using scenario simulations or by using data on previous cyberattacks. This may help the system to better adapt measures for cyber defense.
- System monitoring: the users can observe the performance of the various components of the system and means of a virtual environment or visualization. This may be useful for detecting and analyzing any suspicious activities.
- Incident handling: for appropriate response actions, it is important to comprehend the current scenario by either spotting any issues or inspections which may elucidate any possible cyber incidents. This may help the user in drawing an in-depth analysis of the situation like identifying the sources of any attacks or the later possible consequences of an attack.
1.2 Definition