Implement defensive techniques in your ecosystem successfully with Python
Key Features
- Identify and expose vulnerabilities in your infrastructure with Python
- Learn custom exploit development.
- Make robust and powerful cybersecurity tools with Python
Book Description
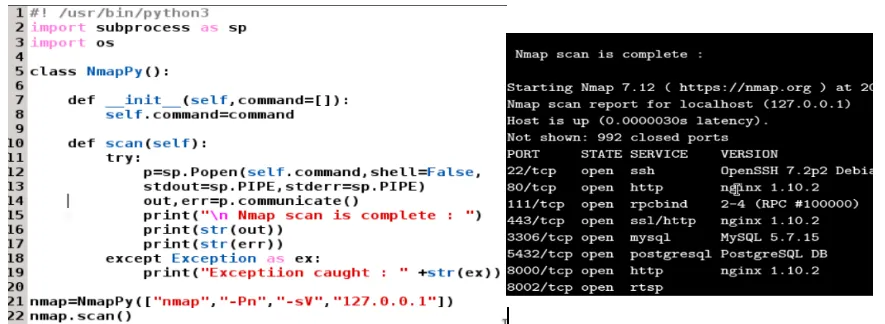
With the current technological and infrastructural shift, penetration testing is no longer a process-oriented activity. Modern-day penetration testing demands lots of automation and innovation; the only language that dominates all its peers is Python. Given the huge number of tools written in Python, and its popularity in the penetration testing space, this language has always been the first choice for penetration testers.
Hands-On Penetration Testing with Python walks you through advanced Python programming constructs. Once you are familiar with the core concepts, you'll explore the advanced uses of Python in the domain of penetration testing and optimization. You'll then move on to understanding how Python, data science, and the cybersecurity ecosystem communicate with one another. In the concluding chapters, you'll study exploit development, reverse engineering, and cybersecurity use cases that can be automated with Python.
By the end of this book, you'll have acquired adequate skills to leverage Python as a helpful tool to pentest and secure infrastructure, while also creating your own custom exploits.
What you will learn
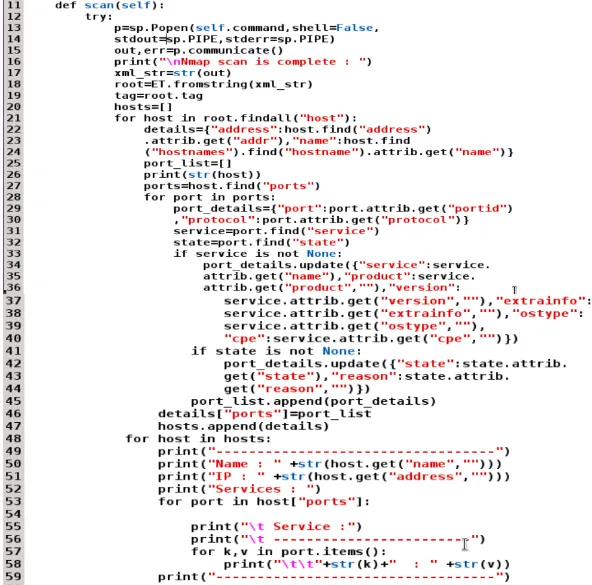
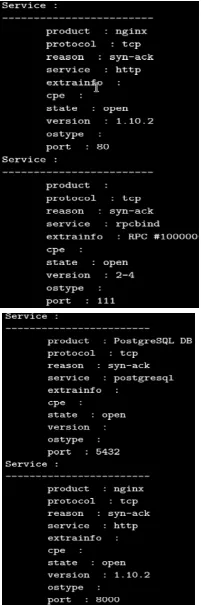
- Get to grips with Custom vulnerability scanner development
- Familiarize yourself with web application scanning automation and exploit development
- Walk through day-to-day cybersecurity scenarios that can be automated with Python
- Discover enterprise-or organization-specific use cases and threat-hunting automation
- Understand reverse engineering, fuzzing, buffer overflows, key-logger development, and exploit development for buffer overflows.
- Understand web scraping in Python and use it for processing web responses
- Explore Security Operations Centre (SOC) use cases
- Get to understand Data Science, Python, and cybersecurity all under one hood
Who this book is for
If you are a security consultant, developer or a cyber security enthusiast with little or no knowledge of Python and want in-depth insight into how the pen-testing ecosystem and python combine to create offensive tools, exploits, automate cyber security use-cases and much more then this book is for you. Hands-On Penetration Testing with Python guides you through the advanced uses of Python for cybersecurity and pen-testing, helping you to better understand security loopholes within your infrastructure.